CHAPTER 4
INTELLIGENCE, SURVEILLANCE, AND RECONNAISSANCE OPERATIONS
All tank and mechanized infantry battalion task forces conduct ISR operations to produce intelligence on the enemy, environment (to include weather and terrain), and civil considerations necessary to assist the commander in developing situational understanding and making decisions. ISR operations require fully developed plans that begin during mission analysis. ISR operations are a commander's function supported by the entire staff and subordinate units. ISR develops, synchronizes, and integrates intelligence from a multitude of collection sources. These operations are multifaceted, and their integration eliminates unit and functional "stovepipes" for planning, reporting, and processing information and producing intelligence. ISR operations must be nested from division to battalion levels. Integration of division cavalry or reconnaissance assets with the TF and brigade assets ensures security and the ability to maintain the initiative.
Section I. FUNDAMENTALS OF INFORMATION COLLECTION
MANAGEMENT
The TF conducts ISR operations first to answer the CCIR (Figure 4-1) and second to facilitate targeting and fill voids in information. Timely and accurate intelligence encourages audacity and can facilitate actions that may negate enemy superiority in soldiers and materiel. Timely and accurate intelligence normally depends on aggressive and continuous ISR. To meet these needs, a fully developed ISR order is required. Understanding the fundamentals of collection management is key to the development of an effective ISR order. This chapter describes the fundamentals of information collection management and other collection assets, techniques for ISR planning, and tactics, techniques, and procedures (TTP) for ISR execution (see FM 3-90, Chapters 12 and 13).

Figure 4-1. Commander's critical information requirements.
4-1. COLLECTION MANAGEMENT
Collection management is a cyclic process that seeks to define what information is required, determine the best method to collect the information, allocate assets to gather information, disseminate intelligence derived from that information to commanders and staff, assess the value of intelligence, and ultimately repeat the cycle. The result is a continuous feed of relevant information that facilitates the commander's situational understanding that ultimately allows him to make better decisions. The collection management process is shown in Figure 4-2. ISR is a continuous process that involves the entire staff. The TF S3 is the chief ISR integrator. He is assisted primarily by the S2 in concert with the remainder of the staff. The TF XO supervises synchronization of the ISR plan and its subsequent execution.
a. Step 1: Develop Requirements. The development of ISR requirements begins with the task force's receipt of brigade WARNOs and eventually the brigade OPORD. At this early stage in the operations process, the TF commander and staff begin to identify gaps in information. These gaps, or information requirements, are the beginning of what will become the ISR plan. Some gaps in information may be answered through RFIs to higher headquarters. Other uncertainties about the enemy and terrain can be answered with the task force's organic ISR assets in order to continue planning and eventual execution. During mission analysis, the commander, assisted by the staff, develops initial PIR and IR. These information requirements will constitute the majority of the initial ISR plan and send out the scouts. It is from this initial ISR plan that all future requirements will be added.
(1) Mission analysis results in situation templates and an event template. This initial event template is primarily composed of named areas of interest (NAIs) that will focus only on identifying which of the predicted enemy courses of action (ECOAs) the enemy has adopted. Upon completion of the mission analysis brief, or as apart of the brief, the commander approves the initial ISR plan and preliminary reconnaissance can begin. As the staff continues with the MDMP, the reconnaissance effort answers information requirements This information assists the commander to validate or refine his visualization. Refinement or a change in visualization based on new information may generate new requirements for the ISR effort.
(2) Once COA analysis is complete, the event template is refined to support friendly decision-making, resulting in the decision support template (DST). This matured event template and DST graphically illustrate in time and space the NAIs and the target areas of interest (TAIs) that are linked to the commander's decision points (DPs). The NAIs, TAIs, and DPs expressed on the DST link the things the commander needs to know with the geographical location where the information may be found and the time the information is likely to be available. These new information requirements (approved CCIR, DPs, and their supporting architecture) constitute the remainder of the ISR plan and are sent to ISR assets either digitally or FM.
(3) Other sources of information requirements include specific orders and requests (SOR) for information from a higher headquarters; specific requests for intelligence or information may come from subordinate or adjacent units. These IR are also incorporated into the ISR plan, which should specify—
- WHAT (activity or indicator).
- WHERE (NAI or TAI).
- WHEN (time that the indicator is expected to occur and the latest time the information is of value [LTIOV]).
- WHY (justification—what decision is the PIR linked to).
- WHO (who needs the results).
(4) When all of the intelligence requirements and PIRs are gathered, they are sorted to reduce redundant requirements and prioritized to assist in allocating resources. The commander then re-evaluates each requirement and finalizes his CCIR.
(5) Ideally, each intelligence requirement will be sufficiently detailed and specific to allow collection. In many cases, the IR will have to be broken down into specific information requirements (SIR) sets that ask very specific questions about indicators. These indicators are tasked to collectors, and taken together they answer the larger question. For example: one of the TF commander's PIR is "will the enemy regiment attack through AA2 with battalions abreast, or from the march? (Triggers repositioning of TF2 into BP1A)." This is a broad question and many indicators could lead to its answer. SIR to support this PIR might include—
- Will enemy units of 3-5 combat vehicles enter NAIs 11, 12, and 13 between 130400MAR and 130700MAR?
- Will enemy battalion #2 move from its assembly area at NAI 7 prior to 130230MAR?
- Identification of second enemy battalion (over 40 BMP2s) in NAI 11, 12, or 13.
b. Step 2: Develop the Collection Plan. The development of the ISR plan follows the same construct as COA development of the maneuver plan; therefore, its development is a collaborative effort between the S3 and S2, supported by the remainder of the staff. It is based on the commander's information requirements and guidance for reconnaissance (see Paragraph 4-3) as well as the products produced in IPB. The TF XO supervises overall development and synchronization of the ISR plan. After identifying the SIR that will answer the PIR and intelligence requirements, the S3, in cooperation with the S2 and the entire staff, begins to develop the collection plan. The staff plans to task assigned or attached assets, requests support from higher headquarters, and recommends tasking to subordinate echelons.
(1) The planners begin to match requirements with specific collection assets based on the following factors.
(a) Availability. Determine what assets are organic and readily available. When will attachments arrive? What systems are not fully mission-capable and when will they be repaired? What are the maintenance and crew rest requirements? What systems are available in higher, adjacent, and subordinate units? How long will it take the asset to get into position?
(b) Capability. Determine if the asset can answer the questions asked? Does it have sufficient range? Can it operate in the expected climate and visibility conditions? Will it be necessary to maintain contact with the target when it is identified? (c) Vulnerability. What is the threat's ability to locate, identify, and destroy the collector both at the target area and on the route to and from the mission? Is the risk of loss greater than the potential gain of information? Will the asset be needed for other subsequent operations? (d) Performance History. How reliable is the specific asset based on training, leadership, and past experience. Who are the "work horses" that can get the job done?(2) The staff develops the collection strategy taking into account the following concepts.
(a) Cuing. Cuing involves the use of one or more sensor systems to provide data that directs collection by other systems. For example, sweeping the battlefield electronically with a wide area surveillance system such as GSR reveals activity that triggers direct collection by a more accurate, pinpoint sensor system such as an unmanned aerial vehicle (UAV).
(b) Redundancy. Redundancy involves the application of several identical assets to cover the same target. Use redundant tasking against HPTs when the probability of success by any one system is low. For example, several scout teams infiltrate over different routes when the risk of detection is high but no other systems are capable of collecting the required information.
(c) Mix. Mix refers to planning for complementary coverage by a combination of assets from multiple disciplines. Sensor mix increases the probability of collection, reduces the risk of successful enemy deception, facilitates cueing, and provides more complete reporting. For example, thermal imagery from a UAV may indicate several vehicle-like hot spots in a suspected enemy battle position (BP). A scout team observing the same NAI may reveal that half of those hot spots are actually decoys and not enemy armored vehicles.
(d) Integration. Integration is the resource management aspect of collection strategy development. Barring a decision to use redundant coverage of a critical target, attempt to integrate new requirements into planned or ongoing missions. Integration helps avoid the common problem of under-tasking very capable collectors. During limited periods of time, collection capability may exceed that of the taskings. The TF commander can resolve this by re-evaluating each of his collection assets for excess capability; focusing excess collection capability on the most important of the remaining unfulfilled requirements; and finally redirecting assets to maximize support to the most important requirements—new or old.
(3) Once an asset is chosen to collect information for an IR, planners turn the SIR into an SOR. The SOR is a directive statement that tailors the reporting criteria to the collection capabilities of the tasked asset. For example:
- An SIR may ask: "Is the enemy artillery battalion (over 12 2S1s) located in NAI 8 between 04800 and 052000MAR?"
- An SOR to a scout team might state: "Report the presence of 2S1 artillery systems in NAI 8 between 04800 and 052000MAR. LTIOV: 052200MAR."
- An SOR to a signal intercept team might state: "Report presence of communications nodes linked to a fire direction net operating in NAI 8 between 04800 and 052000MAR. LTIOV: 052200MAR."
(4) SORs are prioritized for each specific asset. An SOR that is the number one priority for the UAV may be a lower priority for GSR.
(5) Once the staff has completed the ISR COA, it synchronizes the plan with the remainder of the BOS (see paragraph 4-6, ISR Order Development). This step is critical not only to ensure collection occurs at the right time and place but also to ensure it is supported appropriately. It is this step which sets the stage for successful ISR operations.
c. Step 3: Task or Request Collection. The primary means of tasking collection assets is the ISR order. The ISR order is published prior to the completed TF order or as part of WARNO #2 and WARNO #3 in order to start reconnaissance as soon as possible and answer the commander's information requirements.
(1) Task Collection. The method used to task collection is time-dependant. In a time-constrained environment, tasking to the scout platoon and other ISR assets, as discussed in step 1, may be as simple as an ISR graphic and order matrix. When a more deliberate planning process occurs, it is preferable for ISR assets to be briefed by the TF staff in addition to receiving the ISR graphics and order. Upon completion of COA analysis and maturation of the ISR plan, FRAGOs are used to retask assets already conducting operations and to adjust ISR execution.
(2) Request Collection. The S2 sends SOR to higher headquarters in the form of an RFI and ensures that the status of those requests are tracked and answered to support the PIR. Additionally, the S2 utilizes intelligence reach operations to obtain information directly related to PIR and SIR from existing databases at adjacent units, higher echelons, and national level.

Figure 4-2. Collection management cycle.
d. Step 4: Disseminate. The ultimate goal of the dissemination process is to get the right information in the hands of the TF commander in time for him to make the decision. Planners arrange direct dissemination from the collector to the requestor. Whenever possible, write into the SOR the requirement for direct dissemination of information to the requestor. For example, information regarding NAI 1 that triggers a targeting decision at TAI 1 (employment of the TF's allocation of CAS) should go to the TF commander as well as the FSO, ALO, and S2 to determine if it answers the CCIR and is what the TF commander wants to target. A well-synchronized ISR plan directs the collectors as to what nets to use to pass on information and to whom. The plan should detail when to use a net call, use of precedence coding (flash, priority, and so forth), and dissemination using digital systems. Perishability is a key consideration in dissemination. At the TF level most information generated during execution is combat information and requires immediate dissemination to the commander.
e. Step 5: Evaluate Reporting. As the operation progresses, the TF XO monitors as the S2 tracks the status of each SOR and begins to analyze SIR and ultimately PIR. They pay particular attention to which assets are not producing the required results. It is very likely that the staff's assumptions about the enemy COAs will not prove entirely correct. This may result in changes to the intelligence requirements or adjustments to the collection timeline. The XO, S2, and S3 assess the value of the information from collection assets and refine SORs to fill in gaps during execution.
f. Step 6: Update Intelligence, Surveillance, Reconnaissance Planning. As with all operations, the collection plan will rarely survive contact with the enemy and will require adjustment during execution. The following factors could drive changes to the collection plan:
- An SOR is satisfied or overcome by events, freeing an asset for other operations.
- A single asset has unexpected success, freeing redundant assets for other operations.
- An asset cues the collection manager but requires confirmation that requires dynamic retasking of other assets.
- The timing of the operation has become desynchronized, requiring modification of LTIOV or changes to prioritization.
- The commander generates new intelligence requirements as the COA evolves and the enemy situation develops.
- Higher headquarters FRAGOs the TF into an unplanned operation.
4-2. TIERS OF RECONNAISSANCE
Tiers of reconnaissance are procedures that are used to better illustrate how ISR operations contribute to the commander's ability to see the battlefield and what types of information (CCIR and IR) are needed and when. Tiers of reconnaissance are based on offensive reconnaissance planning. (See Figure 4-3.)
(a) Tier 1. Tier 1 reconnaissance occurs before the operation commences and primarily answers voids in information (IR). Tier 1 reconnaissance generally entails basic scout missions (route and zone reconnaissance) that facilitate the unit getting from the assembly areas (AAs) or attack positions to the objective.
(b) Tier 2. Tier 2 reconnaissance occurs preferably before, but may also occur as, the main body begins execution. Tier 2 confirms the enemy's COA and validates the TF base plan of attack. Tier 2 answers CCIR (such as: DP-Tiger Strike North or Tiger Strike South) but also answers IR (maneuver event-driven targeting) that support TF indirect fire planning.
(c) Tier 3. Tier 3 is primarily surveillance and occurs during the operation. Tier 3 confirms the enemy's reaction to our base plan (his branches) and provides the commander the critical information (CCIR) he needs to make decisions (DPs). Tier 3 DPs are usually maneuver-based (such as DP-Tiger Trap North) or targeting-based (DP to commitment of FA or air assets to destroy an HVT).
(d) Tier 4. Tier 4 reconnaissance occurs after the decisive operation. While Tier 3 is both reconnaissance (focused on future operations, generally answering IR) and surveillance (maintaining contact with the enemy), Tier 4 restarts the reconnaissance "cycle."
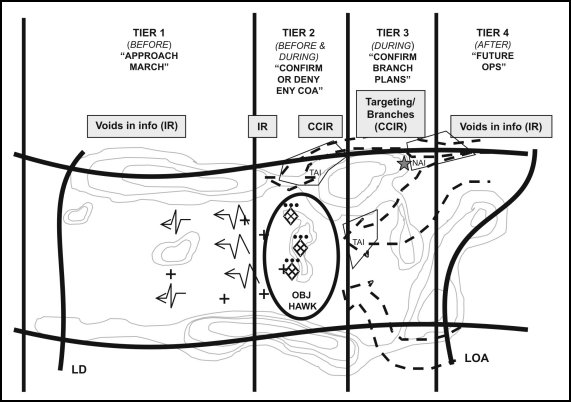
Figure 4-3. Tiers of reconnaissance.
4-3. RECONNAISSANCE OPERATIONS
Reconnaissance is a mission designed to obtain information on the enemy or characteristics of a particular area. Reconnaissance is the precursor to all operations and may be accomplished through passive surveillance, technical means, human interaction, or by fighting for information. (See FM 17-95.) Successful reconnaissance operations are planned and performed with six reconnaissance fundamentals in mind.
(a) Orient on the Reconnaissance Objective. The commander focuses the reconnaissance effort on the specific (critical) areas or objectives for which information is needed. The reconnaissance objectives are based on the PIR established by the commander and serve to prevent wasted effort and time on areas that are not important to the planning and decision cycle.
(b) Maximize Reconnaissance Assets. The TF must seek ways to include all of its subordinates into the reconnaissance and surveillance (R&S) effort and include those instructions and requirements in the OPLAN.
(c) Gain and Maintain Contact. Contact with the enemy or reconnaissance objective is critical to collecting information. Once contact is established, the enemy or location is continuously monitored until information about it is no longer required. Contact must be maintained until the requirement is met or contact is handed over from one observer to the next. Close coordination is required in passing an enemy from one observer to another and eventually to the follow-on maneuver elements.
(d) Develop the Situation. During reconnaissance operations, it is important to rapidly gain situational understanding to provide the commander with the information he needs to effectively maneuver the TF. Reconnaissance assets must be prepared to alter their plans and react to a changing battlefield environment in support of the commander's intent. This may require them to adjust execution as the situation becomes clearer.
(e) Report all Information Rapidly and Accurately. Combat information is extremely time sensitive; information loses its relevance as it ages. The commander and staff develop a plan to employ the TF based on information requirements that must be fulfilled. Delayed, inaccurate, or misdirected information may lead to missed opportunities or poor decisions. The SIRs developed by the S2 help subordinates focus on the information required for decision making.
(f) Retain Freedom of Maneuver. The ability to maneuver is essential to reconnaissance operations. Planners must anticipate tactical developments and constantly develop COAs that avoid decisive engagement of reconnaissance assets and preserve them for future operations. Reconnaissance assets that become engaged usually fail in their primary task, are unavailable for subsequent tasks, and often risk bringing on a larger engagement not envisioned by the commander.
4-4. REconnaisSance Guidance
The commander must provide specific guidance to the reconnaissance force. The commander's guidance for reconnaissance includes focus, tempo, and engagement criteria. This guidance is an extension of the commander's intent and is designed to focus the reconnaissance commander's efforts in relationship to the TF mission.
a. Focus. Focus is the expression of what types of information the TF commander is most concerned with. The commander's focus for reconnaissance usually falls in three general areas: CCIR, targeting, and voids in information. The commander's focus allows reconnaissance to prioritize taskings and narrow their scope of operations. An operation may have a terrain focus where status of routes, bridges, and obstacles are more important than the enemy. Conversely, the operation may focus on the enemy where locating his security zone, main body, and reserves are essential. Additionally, commanders may express their focus in terms of reconnaissance pull and push.
(1) Reconnaissance Pull. Reconnaissance pull is used when the enemy situation is not well known and or the situation is rapidly changing. Reconnaissance pull fosters planning and decision-making based on changing assumptions into confirmed information. Initial assumptions and PIR are used to deploy reconnaissance assets early to collect information for use in the development of COAs. The commander uses ISR assets to confirm or deny initial PIRs prior to the decision on a COA or maneuver option, thus pulling the TF to the decisive point on the battlefield. Success of the reconnaissance pull requires an integrated reconnaissance plan that can be executed prior to the commander having to make a COA decision.
(2) Reconnaissance Push. Reconnaissance push is used once the commander is committed to a COA or maneuver option. The commander pushes his ISR assets forward, as necessary, to gain greater visibility on specific NAIs to confirm or deny the assumptions on which the COA is based. Information gathered during reconnaissance push is used to finalize the TF plan.
b. Tempo. The commander establishes the time requirements he envisions for the reconnaissance force and expresses them in a statement that describes the degree of completeness, covertness, and potential for engagement he is willing to accept. The following describes the rate TF commanders use to control the momentum of reconnaissance operations.
(a) Deliberate. Operations are slow, detailed, and broad-based. They require the accomplishment of numerous tasks. This is a description of the degree of completeness required by the commander. Significant time must be allocated to conduct a deliberate reconnaissance.
(b) Rapid. Operations are fast paced, focused on key pieces of information, and entail a small number of tasks. This is a description of the degree of completeness required by the commander. It describes reconnaissance operations that must be performed in a time-constrained environment.
(c) Stealthy. Operations are conducted to minimize chance contact and prevent the reconnaissance force from being detected. They are often conducted dismounted and require increased allocation of time for success. This is a description of the level of covertness required by the commander.
(d) Forceful. Operations are conducted without significant concern about being observed. They are often conducted mounted or by combat units serving in a reconnaissance role. It is also appropriate in a stability or support operation where the threat is not significant in relationship to the requirement for information. This is a description of the level of covertness required by the commander.
(e) Aggressive. Operations have very permissive engagement criteria and allow the reconnaissance commander to engage in combat to meet his IRs. This is a description of the potential for engagement.
(f) Discrete. Operations have very restrictive engagement criteria and restrain the reconnaissance forces from initiating combat to gain information. This is a description of the potential for engagement.
c. Engagement Criteria. The commander establishes what enemy forces he expects reconnaissance forces to engage and with what level of force. This decision assists the reconnaissance leadership in planning direct and indirect fires and establishing bypass criteria. It is particularly important when the reconnaissance force is augmented with combat systems to conduct reconnaissance in force or security operations.
4-5. FORMS OF RECONNAISSANCE
To logically group SIRs and tasking into missions for subordinate commanders, the TF commander uses one of four forms of reconnaissance. (See FM 17-95.) The forms of reconnaissance serve to further refine the scope of the reconnaissance commander's mission and give it a spatial relationship. The four forms of reconnaissance are route, area, zone, and reconnaissance in force.
a. Route. A route reconnaissance is an operation focused on obtaining detailed information on a specific route and all adjacent terrain from which the enemy could influence the route. The route may be a road or an axis of advance. Route reconnaissance is performed to ensure that the route is clear of obstacles and enemy, and that it will support planned movement. A route reconnaissance may be performed as part of an area or zone reconnaissance. There following are critical tasks associated with a route reconnaissance:
- Assess trafficability of the route.
- Locate enemy forces that can influence movement on the route.
- Identify lateral routes in the area of responsibility.
- Classify bridges.
- Identify overpasses, underpasses, and culverts that might restrict access.
- Clear or locate bypasses to any defiles.
- Locate mines, obstacles, or barriers.
- Locate bypasses around built up or contaminated areas.
b. Area. An area reconnaissance is a directed effort to obtain detailed information concerning the terrain or threat activity within a prescribed AI. The reconnaissance of the area can be conducted by maneuvering elements through the area or by establishing observation posts (OPs) within or external to the AI. See paragraph c below for critical tasks associated with an area reconnaissance.
c. Zone. A zone reconnaissance is a directed effort to obtain detailed information concerning all enemy forces, routes, obstacles, and terrain within a zone defined by boundaries. A zone reconnaissance is assigned when the situation is vague or when information about cross-country trafficability is desired. It is appropriate when previous knowledge of the terrain is limited or when combat operations have altered the terrain. The reconnaissance may be enemy-oriented or terrain-oriented. A zone reconnaissance is deliberate and time consuming. Critical tasks associated with both zone and area reconnaissance include the following:
- Determine location and strength of enemy forces.
- Reconnoiter terrain for its impact on the operation.
- Locate and determine the extent of contaminated areas.
- Locate bypasses to all natural or manmade obstacles.
- Classify all bridges, underpasses, overpasses, and culverts.
- Conduct route reconnaissance as required.
d. Reconnaissance in Force. A reconnaissance in force is a deliberate combat operation designed to discover or test the enemy's strength, dispositions, and reaction or to obtain other information. A commander uses a reconnaissance in force when the enemy is known to be operating within an area and the commander cannot obtain adequate intelligence by other means. A unit may also conduct a reconnaissance in force in restrictive terrain where the enemy is likely to ambush smaller reconnaissance forces. A reconnaissance in force is an aggressive reconnaissance, conducted as an offensive operation in pursuit of clearly stated CCIR. The overall goal of a reconnaissance in force is to determine enemy weaknesses that can be exploited. It differs from other reconnaissance operations because it normally is conducted only to gain information about the enemy and not the terrain. The TF requires significant augmentation with combat elements to conduct a reconnaissance in force. Specific tasks include the following:
- Penetrate the enemy's security zone to determine its size and depth.
- Determine the location and disposition of enemy main positions.
- Attack the enemy main positions to cause the enemy to react with local reserves, counterattack forces, fire support assets, or specific weapon systems.
- Determine weaknesses in enemy dispositions that can be exploited.
Reconnaissance is the precursor to all operations. As such the development of the ISR order (Step #9 Mission Analysis—Determine the Initial ISR Plan) is one of the most critical steps in the battalion MDMP.
a. The TF's MDMP formally begins with the receipt of the brigade OPORD. However, brigade WARNO #1 and #2 may provide the staff with sufficient information to start IPB. Once the staff receives a finalized COA and specified tasks found in WARNO #3 and the brigade OPORD, it can begin the formal mission analysis. However, when parallel and collaborative planning is used, the commander and staff have already begun to identify initial PIR and IR early in the process. These information requirements are included in the commander's initial guidance to the staff for development of the ISR plan. The commander's initial guidance to the staff includes—
- How to abbreviate the MDMP
- Initial time allocation
- Initial ISR planning guidance to staff and or initial reconnaissance to begin (usually based on required movement).
- Authorized movement
- Additional tasks the commander wants the staff to do.
b. The commander's initial ISR planning guidance includes the commander's initial information requirements based on his analysis and his staff's initial assessment. These information requirements are primarily planning-focused. The staff's mission analysis will yield information requirements from the IPB process. The two basic IPB-generated information requirements are the result of terrain and enemy analysis.
(1) Terrain Analysis. The terrain analysis may generate uncertainties about the terrain that can affect how the battalion plans for the operation. These uncertainties might include—
- Does AA1 support tactical movement?
- Where along AAI must the battalion conduct a defile drill?
- Can the battalion easily ford that creek in multiple places or is it restricted to ford sites and or bridges?
(2) Enemy Analysis. The TF commander and staff develop ECOAs and prioritize them in the order of probability; this, in turn, forms the basis for determining the IRs for the ISR assets. Enemy COAs take the form of situation templates (SITEMPs). Differences between the situational templates form the initial event template. This initial event template focuses only on identifying which of the predicted COAs the enemy has adopted. (See FM 34-130.) The initial event template forms the base of the ISR graphics. Later in the process, the event template will be refined to support the commander's decision-making during execution—the DST. The development of the situation templates and the event template is not the sole responsibility of the S2 but rather is a collective staff task. The following are examples (not all-inclusive) of staff input to ECOA development, SITEMP, and event template development and reconnaissance objectives.
(a) Air Defense—
- Likely air corridors.
- Likely timing of air strikes or air assault operations.
- Likely targets and objectives of enemy air operations.
- How the enemy ADA is organized to protect its forces.
- Whether the enemy will use air in reconnaissance or counterreconnaissance role.
(b) Fire Support—
- Where are enemy target acquisition assets (such as radar)?
- Where will the enemy deploy his artillery?
- Determines high-value targets (HVT) (further develop into HPTs during the war gaming and targeting process).
- How deep can his indirect fires range?
(c) Engineer—
- Where will enemy emplace obstacles (protective, tactical, situational)?
- Time required to emplace each type of obstacle.
- Time required to breach obstacles.
- Time required to entrench a mechanized company.
- Ability to bridge different size rivers and streams and time required for each.
(d) NBC—
- Enemy capabilities to employ NBC weapons and obscurants.
- Types of delivery systems, including minimum and maximum ranges.
- Enemy NBC protection capabilities.
- Indicators of preparations to employ NBC weapons.
- Friendly assets the enemy is likely to consider HPTs for NBC targeting.
- Existing contaminated areas that may indicate the COA adopted by enemy.
(e) Signal—
- Ability to locate or intercept friendly systems.
- Speed that the enemy can collect, process, and target communication and C2 sites.
- Ability to link collection systems to indirect fires.
- Deployment patterns of signals intelligence (SIGINT) collection systems.
- Techniques of electronic deception or network attack.
(f) Civil Affairs (CA)—
- What is the political situation in the AO?
- What factions are friendly, neutral, or enemy?
- Where are areas that civilians gather to protest or demonstrate?
- From whom or where is information gained on particular AOs?
c. Once integration of the ISR plan is completed, it must be synchronized (scheme of support) with the BOS to ensure all provisions are made for its success. Synchronization considerations include:
- Location, mission, and specific instructions regarding brigade reconnaissance troop (BRT) or other higher ISR assets.
- Specific instructions to TF maneuver assets (maneuver support, fire control measures, extraction considerations, for example).
- Required ADA support (ADA warning network, A2C2 measures).
- Required fire support (EFST considerations and coordination measures).
- Required mobility/counter mobility/survivability support.
- Required logistics support to include class III, V, medical, and maintenance.
- Required communications support (long-range communications equipment, retrans, C2 locations, and compatibility, for example).
d. During the mission analysis brief or shortly after, the commander approves the initial ISR plan. Following approval, reconnaissance can begin. In a time-constrained environment, dissemination of the order may be as simple as an overlay and matrix sent to the TF scout platoon and other participating assets via LNO or digital means. However, the preferred method of dissemination is for the staff to brief ISR assets in conjunction with order and graphic dissemination. This method is best because it also provides the TF commander the opportunity to personally convey his focus for reconnaissance to the scout platoon and other assets. The ISR plan will include—
- Brigade mission.
- Brigade commander's intent.
- Reconnaissance objectives for the TF.
- CCIR.
- Focus, tempo, and engagement criteria.
- Specified reconnaissance tasks.
- Fires plan.
- CASEVAC plan.
- Resupply plan.
- Camouflage plan.
e. Under normal circumstances, ISR assets receive the mature ISR plan through FRAGOs that adjust their requirements and execution based on the war game and DST. Additionally, the mature ISR plan is not only included but also integrated into the TF scheme of maneuver to ensure full synchronization between ISR and maneuver:
- The product of mission analysis is used to develop the ISR order.
- The ISR order addresses all aspects of the reconnaissance operation to include insertion methods, supporting fires, casualty evacuation (CASEVAC) and CSS, and extraction contingencies.
- The commander's guidance for reconnaissance includes focus, tempo, and engagement criteria.
- The TF's initial counterreconnaissance plan is also part of the ISR order. Other essential products in the ISR order include the ISR graphical overlay, the enemy SITEMP, and the ISR tasking matrix.
4-7. INTELLIGENCE, SURVEILLANCE, RECONNAISSANCE OVERLAY
The ISR overlay expresses the ISR order in graphic form. If it is transmitted over digital systems, it may need to be broken into component parts to speed transmission and reduce clutter. For example, it could be broken into one overlay showing the basic operational graphics and boundaries, one overlay showing infiltration graphics, and one overlay showing sensor locations and range fans (see Figure 4-4). Regardless of its component parts, the ISR overlay should contain the following:
- Friendly boundaries and phase line (PL).
- NAIs/TAIs.
- LOAs and limits of reconnaissance (LORs).
- Counterreconnaissance AOs for all units.
- FSCM.
- Graphics depicting zone, area, or route reconnaissance.
- Routes, start points (SP), release points (RP), and checkpoints.
- Primary and alternate OP locations.
- Ambulance exchange points (AXP) and logistics release points (LRP).
- Planned or existing obstacles.
- Scan sectors for sensors.
- UAV flight paths.
- Retrans locations.
4-8. ENEMY SITUATION TEMPLATE
The S2 develops an enemy SITEMP for the ISR operation that focuses on the enemy's reconnaissance and counterreconnaissance efforts. It is designed to aid in planning friendly infiltration and survivability by identifying enemy actions that will impact on friendly reconnaissance efforts (see Figure 4-4). The enemy SITEMP should include—
- Locations of known and suspected enemy locations.
- Suspected enemy boundaries.
- Enemy avenues of approach for the main body with time phase lines (TPLs).
- Likely enemy reconnaissance and infiltration routes with TPLs.
- Likely enemy OPs and patrols.
- Enemy artillery range fans.
- Known and templated obstacles.
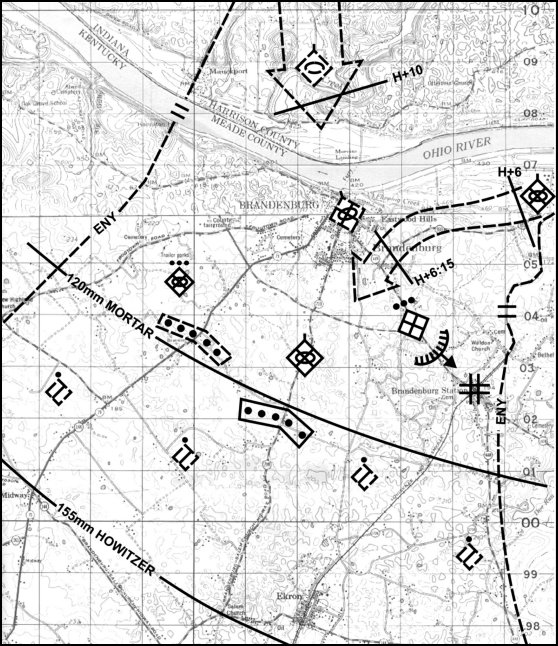
Figure 4-4. Situation template.
4-9. TERRAIN MANAGEMENT
The TF distributes its reconnaissance assets throughout its AO. To prevent fratricide and to synchronize the collection effort and logistic support, the TF must organize the battlefield. When assigning boundaries and task-organizing subordinate units, the TF commander should include the terrain team or engineer leadership in the decision process.
Section II. SECURITY OPERATIONS
The purposes of security operations are to provide early and accurate warning of enemy operations, to provide the protected force with time and maneuver space to react to the enemy, and to develop the situation to allow the commander to employ the protected force effectively. Units may conduct these operations to the front, flanks, or rear of a larger force. Security operations provide reaction time, maneuver space, and protection to the main body. Security operations are characterized by aggressive reconnaissance aimed at reducing terrain and enemy unknowns, gaining and maintaining contact with the enemy to ensure continuous information, and providing early and accurate reporting of information to the protected force. Security operations forces orient in any direction from a stationary or moving force. Security operations are designed to deny the enemy intelligence information concerning the TF. Security operations contain both passive and active elements and normally include combat action to seek, destroy, or repel enemy reconnaissance units. The TF performs three primary types of security missions: screen, guard, and area security. The TF normally participates in covering force operations only as part of a larger element.
4-10. SCREEN
The primary task of a screening force is to observe, identify, and report information. The screening force protects the main body, impedes and harasses the enemy with supporting indirect fires, and destroys enemy reconnaissance elements within its capability.
a. TF Screen. At the TF level, the scout platoon normally performs screen missions. When the terrain provides multiple enemy avenues of approach, the TF commander may attach the scout platoon to a company team to conduct a screen. The screening force generally establishes a series of OPs and conducts patrols to ensure adequate surveillance of the assigned sector.
b. Company Team Screen. A company team may be directed to conduct a screen in support of TF offensive and defensive operations. When given a forward screen mission, the company team moves as in a movement to contact.
c. Planning a Screen. When assigning a screen mission to a company team, the TF commander or operations officer designates the general trace of the screen and the time it must be established. The initial screen line should be forward of the general trace but remain within range of supporting artillery. Screen lines are depicted as phase lines; passage graphics are included in the overlay.
(1) Designate the left and right limits of the screen as well as a phase line for the near boundary. This phase line can also become the on-order BHL.
(2) Confirm which unit has responsibility for the area between the screening force's rear boundary and the main battle area (MBA). This should be the company team that occupies the sectors behind the screen.
(3) Designate general locations for OPs that enable observation of the avenues of approach into the sector.
(4) Select routes or sectors to facilitate rearward displacement.
(5) Augment the security force as needed to provide intelligence, engineer, air defense, signal, and combat service support.
d. Intelligence Support. The S2 designates which NAI the company team must observe and when. The S2 does not dictate the location of company team elements or how the company team maintains surveillance of the NAI. If GSRs operate under TF control to support the security effort, the S2 positions these assets and integrates their locations and missions with the security action of the screening company team. Once the screen force commander positions his unit, he informs the S2 of their primary, alternate, and subsequent locations.
e. Maneuver. Generally, the best unit configuration for the screen mission is a mechanized infantry company team. The ability to place infantry squads on the ground and conduct surveillance operations and active patrolling is an essential passive aspect of the screen mission. The tank platoon may be employed to destroy the enemy's reconnaissance vehicles during the counterreconnaissance fight.
f. Fire Support. The FSO prepares for the screen mission as he would for a defense in sector. He uses the enemy situation template as a guide to plan fires to interdict enemy maneuver elements. He plans protective fires for all screen force positions; this helps prevent screening force elements from becoming decisively engaged with the enemy. Accurate indirect fire is essential to the destruction of the enemy reconnaissance effort. The FSO conducts a time-distance analysis covering the enemy's probable rate of advance and the time of flight of artillery or mortars. If available, Striker teams may be added to the screen force for use against enemy vehicles.
g. Engineer Support. Generally, the engineer effort is dedicated to the TF's main defensive area. If available, some engineer effort may be dedicated to the forward screen. The obstacle plan should not be so severe that it alters enemy movement significantly prior to its engagement by forces in the main battle area. The obstacles found forward of the MBA should be designed to delay enemy reconnaissance elements temporarily and assist in their destruction. Point-type targets along restrictive portions of the enemy's avenues of approach are an example of obstacles that may be bypassed yet offer a target to weapons covering the obstacle.
h. Logistics. The logistics planner must plan for responsive and flexible support that may require the immediate resupply of ammunition and evacuation of casualties and equipment upon contact. Lateral supply routes to each battle position are identified during the planning process. Moreover, on-order control measures, LRPs, UMCPs, and AXPs are essential to the operation. Emergency resupply vehicles carrying ammunition and other quickly expendable supplies, plus refuelers, are prepared to respond to sudden requisitions due to enemy contact. Once the TF begins the fight, evacuation of wounded personnel and damaged equipment occurs along lateral supply routes.
4-11. GUARD
A guard mission is assigned to protect the force by observing the enemy, reporting pertinent information, and fighting to gain time. The guard force differs from a screen force in that it contains sufficient combat power to defeat, repel, or fix the lead elements of an enemy ground force to prevent it from engaging the main body with direct fires. The guard force normally deploys over a narrower front than a comparably sized screening force, allowing greater concentration of combat power. The guard force routinely engages enemy forces with both direct and indirect fires and operates in range of the main body's indirect fire weapons. The guard force commander must understand fully the degree of security his unit provides the larger unit. This understanding is critical because, as the battle progresses, the higher unit commander may require the degree of security to change (for example, from early warning to detailed and aggressive security for the main body). There are three types of guard operations conducted in support of a stationary or moving friendly force: rear, flank, and advance guard (Figure 4-5).
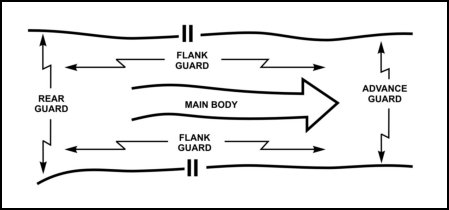
Figure 4-5. Rear, flank, and advance guard operations.
a. Advance Guard. The advance guard moves ahead of the main force to ensure its uninterrupted advance, to protect the main body against surprise, to facilitate its advance by removing obstacles and repairing roads and bridges, and to cover the deployment of the main body as it is committed to action. The advance guard is a task-organized, combined arms unit or detachment that precedes a column or formation.
(1) The advance guard is normally conducted as a movement to contact. Generally, a TF receives an advance guard mission when the brigade moves as part of the division main body in a movement to contact. In deploying an advance guard, the brigade ensures the TF has priority of fires from the DS artillery battalion. Unlike a movement to contact, however, the advance guard clears the axis of enemy elements to allow the unimpeded movement of the TF main body. The security force develops the situation to hand over the enemy to the TF. The advance guard can conduct hasty attacks if it has sufficient intelligence to overwhelm the enemy.
(2) Depending on the commander's estimate of the situation, a TF conducting an advance guard normally conducts a movement to contact with company teams advancing on axes, inAOs, or (rarely) along directions of attack.
(3) Based on METT-TC, trail elements of the advance guard must ensure they maintain adequate distance forward of the main body's lead elements to ensure freedom of maneuver for the main body. The TF commander establishes phase lines to control the movement of the main body and the advance guard. Advance guard units remain within the TF's artillery range.
(4) The advance guard force attempts to destroy enemy forces through hasty attacks. It may be necessary for the TF to mass at certain locations, destroy the enemy, report, and continue with its mission. If enemy resistance is well prepared and cannot be destroyed, the TF reconnoiters to identify a bypass route for the main body, to report enemy size and location, and (when given permission) to fix and bypass the enemy. The following attacking forces are responsible for destroying the bypassed enemy. The main body commander may elect not to bypass the enemy but to conduct a deliberate attack. In this case, the advance guard keeps the enemy contained and prepares to pass main body elements through to eliminate the enemy.
b. Rear Guard. When a division conducting a movement to contact requires rear security, a TF may receive a rear guard mission. The rear guard protects the rear of the main body and all CS and CSS elements in the main body. It may accomplish this by conducting an attack, a defense, or a delay. A TF conducting a rear guard operation follows the same axis of advance as the protected force at a distance prescribed by the main body commander and normally within artillery range. The TF commander establishes company team battle positions or sectors. When using sectors, he designates phase lines and checkpoints to control movement. The rear guard's responsibility begins at the main body rear boundary and extends as far from this boundary as the factors of METT-TC allow.
c. Flank Guard. A TF may receive a flank guard mission during a division movement to contact. The flank guard is responsible for clearing the area from the division main body to the flank guard's designated positions. The TF must be prepared to operate on a frontage that is greater than for other tactical operations. Usually, the area extends from the lead forward screen, along the flank of the formation, to either the forward edge of the battle area (FEBA) or the rear of the moving formation, tying in with the rear guard. Due to the complexities of this operation, the following detailed discussion of flank guard operations is provided.
(1) Templates and Analysis. Once the TF receives a flank guard mission, the S2 determines the type of threat facing the TF during its movement. This information is critical to the commander in his selection of appropriate formation and movement techniques. The IPB must incorporate the entire area of operations with analysis of the mobility corridors and avenues of approach extending from the FEBA to the objective. The S2 produces a situational template and an event template. He develops and inputs an R&S plan with specific reconnaissance objectives for subordinate units as the enemy overlay. Subordinate units verify the S2's situational template during reconnaissance and periodically send enemy overlay updates back to the S2. The staff develops the DST to assist the commander in assessing the situation and making decisions.
(2) Formation and Movement Techniques. From the intelligence estimate the commander determines the formation and movement technique, accounting for the enemy situation and main body disposition. Movement techniques include—
(a) Alternate Bounds. The commander uses this technique when he anticipates strong enemy action against the flank. It requires slow movement by the main body.
(b) Successive Bounds. The commander uses this technique when he expects enemy action against the flank to be light and movement of the main body to include frequent short halts.
(c) Moving Guard. The commander uses this technique when he expects no enemy action on the flank and the main body will move with all possible speed. In the moving guard, an armor heavy company team executes the forward screen mission while traveling as in a movement to contact. The mortar platoon follows the forward screening company team to provide support. The scout platoon, normally with an armor section under operational control (OPCON), conducts a flank screen outside the tentative battle position line. The remaining company teams travel in column, along an axis or in sector, behind the forward screen. The commander uses this technique when the greatest enemy danger appears to be from the front.
(3) Fire Support. The fire support officer plans the flank guard operation the same as any offensive operation. Based on the IPB, he targets those enemy avenues of approach that threaten the force. He targets known and suspected enemy positions along the axis of advance or in the TF zone to support the forward screening element. During the operation, the TF executes its fire support plan as it would in movement to contact and defensive operations. On the forward screen, as the TF encounters enemy positions and subsequently destroys or fixes and bypasses them, it uses artillery to suppress the position. Should the enemy attempt to attack from the flank, the TF executes the fire support plan as it would for defensive operations to support the defense or delay.
(4) Engineer Support. The TF engineer officer in charge of the attached engineer unit has two missions to consider in planning the flank guard mission: mobility and countermobility operations. Engineers are organized as they would be for a movement to contact. Usually, they follow the lead element and assist in negotiating any obstacles that prevent continued advance. The obstacle plan should include rapidly emplaced obstacles through a family of scatterable mines (FASCAM), ground-emplaced mine scattering system (GEMSS), or other assets. Engineers also identify key bridges or other potential obstacles during the planning process so they can render them unusable for enemy maneuver. Above all, the engineers develop a plan allowing the responsive emplacement of obstacles on short notice.
(5) Air Defense. The ADO develops a flexible plan to allow for the protection of the force as it changes posture between moving and stationary. He plans the TF air defense as he would in an offensive operation. Most assets are attached to maneuver elements and the main CP. Route protection or other areas go without support or rely on protection from main body ADA assets. The TF executes the air defense plan as in a movement to contact where a moving force may need to adopt a hasty defense quickly. Whether moving or stationary, air defense assets must be linked to the main body's air defense early warning net and the positioning of assets must protect not only the flank guard but also approaches into the main body.
(6) Logistics. The logistics planner has the same difficulties as in planning a movement to contact. He must plan for responsive and flexible support that may require the immediate resupply of ammunition and evacuation of casualties and equipment upon contact. The planner identifies lateral supply routes to each battle position during the planning process. On-order control measures, LRPs, UMCPs, and AXPs are essential to the operation. As the TF begins its movement, the TF trains should travel abreast of the flank guard unit (close to the main body) to avoid exposing CSS elements to the enemy. Emergency resupply vehicles carrying ammunition and other quickly expendable supplies, plus refuelers, are ready to respond to sudden requisitions due to enemy contact. Once the TF begins the fight, evacuation of wounded personnel and damaged equipment occurs along lateral supply routes all the way to the main body if that is where the support TF is located. Otherwise, the evacuation is back along the axis of advance.
(7) Orientation of Forces. A unique aspect of the flank guard mission is the orientation of the forces and the direction they may be ordered to screen. While the force maneuvers forward along its assigned axis of advance or zone, phase lines control the movement of the company team elements. There should be a phase line on either side of each company team's battle position. The battle positions are generally larger than in a purely defensive mission, partly due to the large frontage the TF must cover. Once an element detects the enemy and company teams adopt hasty defensive positions, these phase lines become boundaries for controlling the defensive battle. This gives the TF commander the option of designating company team sectors in addition to the battle positions already identified. Similarly, control of the reserve is accomplished through phase lines and checkpoints regardless of the actual direction of the maneuver. As a minimum, the following control measures are included:
- Phase lines (revert to boundaries on contact).
- Battle positions.
- Target reference points (TRPs).
- Axis of advance.
- Axis of advance of main body.
- Objectives (if used).
4-12. AREA SECURITY
Area security refers to a force's mission to secure a specific area. Area security actions could include area reconnaissance and security of designated personnel, equipment, facilities (including airfield and seaports), main supply routes, lines of communication, and critical points. The TF is most often employed as an advance guard for a brigade, as part of a covering force for a division, or as an area security force during a stability or support action.
4-13. COVER
A covering force accomplishes all the tasks of screening and guard forces. Unlike screening or guard forces, a covering force is tactically self-contained and capable of operating independently of the main body to develop the situation early and deceive, disorganize, and destroy enemy forces. Cover may be an offensive or defensive mission. The requirements placed upon the covering force, the command and control structure necessary for the forces involved, and the large areas of operations involved require an adequate level of command for successful accomplishment. The TF performs screen and guard missions. Covering force operations are normally an armored cavalry regiment mission for the corps or a task-organized brigade for the division. A covering force, or portions of it, often becomes decisively engaged with enemy forces; therefore, the covering force must have substantial combat power to engage the enemy and still accomplish its mission. FA, engineers, air defense, intelligence resources, and CSS should be planned to support the cover mission.
Section III. RECONNAISSANCE
Reconnaissance and surveillance assets obtain information about the enemy or the physical makeup of a particular area by visual or other detection methods. Successful R&S collects quick, accurate information about the enemy and terrain. R&S plans are designed to tell the commander what he needs to know in time for him to act and do as much as possible ahead of time. R&S is part of a larger, ongoing collection process that receives its direction from the mission, the commander's need for information, and, by extension, the IPB process. These processes outline the who, what, where, when, and why of collecting intelligence.
4-14. TASK FORCE RECONNAISSANCE AND SURVEILLANCE
TF reconnaissance and surveillance operations are a broad category of activities designed to support TF intelligence development, planning, and decision-making. Reconnaissance is a combined arms maneuver operation that employs the TF's reconnaissance assets to use visual or other detection methods to observe NAIs and TAIs in order to collect combat information. Surveillance involves the systematic observation of an NAI by visual, electronic, photographic, or other means. The TF S2 section analyzes and evaluates combat information collected by the scout platoon and other assets, resulting in combat intelligence. The goal of combat intelligence is to answer the TF commander's priority intelligence requirements and other intelligence requirements to enable timely and effective decision-making.
4-15. FUNDAMENTALS
Successful TF reconnaissance depends on the following fundamentals:
- Appropriate reconnaissance forward.
- Reconnaissance focused on PIR, IR, and DPs.
- Reconnaissance initiated early and conducted continuously.
- Integration of TF reconnaissance with brigade reconnaissance.
- Integration of the staff in reconnaissance planning.
- Reconnaissance planned from the beginning.
- Maximized reconnaissance assets.
- Information reported, analyzed, and disseminated rapidly and accurately.
a. Appropriate Reconnaissance Forward. Commanders normally do not hold scout platoons and reconnaissance assets in reserve. The fluid and nonlinear nature of the modern battlefield requires that reconnaissance be continuous and aggressive throughout the AO. In some situations, the critical reconnaissance objectives may not be forward of the maneuver forces.
b. Reconnaissance Focused on PIR, IR, and DPs. The reconnaissance or collection plan should focus on the collection of information required to support the PIRs and provide observation of the decision points on the battlefield. The PIR derived from the commander's critical information requirements identify the information on the enemy that the commander needs to support his battlefield visualization and to make critical decisions. The PIR help the commander filter information available to him by defining what is important to mission accomplishment. The commander and S2 use PIR to focus collection efforts, which is vital considering the limited number of reconnaissance assets available at the TF level. Focusing the reconnaissance ensures that the commander's PIR and IR are answered and prevents waste of assets used in looking for the wrong information. In addition to TF PIR, there are also PIR from the brigade and higher that influence the focus of TF reconnaissance efforts.
c. Reconnaissance Conducted Continuously and Early. Reconnaissance, surveillance, and security are continuous processes that should be conducted 24 hours a day. For security and surveillance missions, the scout platoon should be augmented with elements from maneuver company teams. The TF S2 should also make full use of broadcast dissemination from brigade to answer PIRs.
d. R&S Staff Integration. The S2 and S3 rely upon the entire staff to assist in the planning and execution of the TF reconnaissance and surveillance plan.
(1) The signal officer apprises the S2 of enemy collection and target capabilities and vulnerabilities of friendly R&S assets.
(2) The FSO coordinates indirect fires to support R&S assets and recommends necessary restrictive fire measures for troop safety.
(3) The commander or platoon leader of a designated R&S asset plans fires and targets for the element.
(4) The engineer platoon leader collects and reports information on terrain and obstacles.
(5) The air defense platoon or section leader plans air defense for the R&S assets and provides information on expected or occurring enemy air activity.
(6) The NBC officer requests and coordinates for NBC data collection and apprises the S2 of any NBC obstacles critical to R&S units in their missions.
(7) The ALO provides air movement and close air support, if requested.
(8) Combat service support considerations for R&S include—
(a) Developing TSOPs for load plans of outposts, to include—
- Establishing CSS procedures for both mounted and dismounted reconnaissance missions.
- Establishing CSS procedures for air versus ground insertion of reconnaissance assets.
- Developing procedures for both aerial and ground sustainment.
(b) Developing resupply techniques, to include—
- Using multiple and or false landing zones away from outposts as cache drop-off points.
- Predetermining the locations and times for resupply of Classes I, III, IV, V, VII, and XI.
- Establishing locations for caches on successive missions and or insertions.
(9) Combat health support considerations include—
- Determining the HSS requirements.
- Deploying trauma specialist and medical assets in DS of reconnaissance operations, as required and appropriate.
- Planning for CASEVAC/extraction operations.
- Developing HSS SOP for supporting reconnaissance elements deployed deep into enemy territory.
- Selecting evacuation sites. (Remember that all cache sites are potential casualty evacuation sites.)
- Developing TTPs for cross-forward line of own troops (FLOT) casualty extraction.
- Establishing the time for pick up and the pickup point for aerial extraction of casualties. (The last known or reported location is normally the aerial pickup point and the best time is 30 minutes prior to beginning morning nautical twilight [BMNT] or 30 minutes after ending evening nautical twilight [EENT].)
- Developing a detailed plan for ground extraction, to escort to casualty exchange point.
- Conducting rehearsals for day and night extractions.
- Requesting escort.
If a member or members of the reconnaissance element become casualties during reconnaissance missions, initial care will be self-aid, combat lifesaver (CLS) advanced first aid, or EMT from a trauma specialist. Trauma specialists may be deployed as a rider in one of the scout vehicle or an ambulance team may be in support. See FM 4-02.4 for additional information on providing HSS for the reconnaissance elements.
e. Maximize Reconnaissance Assets. The TF must maximize the capabilities of its limited reconnaissance assets. It must ensure that collection requirements specify exactly what needs to be collected and where and when it needs to be collected and reported for the TF to conduct its operations. Additionally, the TF S2 must make sure he does not send the scout platoon to obtain information that may already be available through brigade assets. Close coordination and integration with the brigade S2 is required to ensure that the brigade and TF assets are not being double-tasked to find the same information.
f. Rapid and Accurate Reporting, Processing, and Dissemination. The TF scout platoon and other assets tasked to conduct reconnaissance must report what they observe accurately and in a timely manner. Digitization speeds both the accuracy of the intelligence gathered as well as the timeliness with which it can be sent. Once the combat information arrives, the TF S2 rapidly evaluates and disseminates it to the company teams and passes it on to the brigade. He does so over FM voice or digitally through remote workstations (RWSs) and FBCB2.
4-16. CAPABILITIES
The scout platoon is the TF's primary means of conducting reconnaissance and surveillance. The scout platoon provides early warning and helps control movement of the TF or its elements. The scout platoon is normally under TF control but may be attached to another unit in the TF for certain operations. The reconnaissance elements are finders, not fighters. They are the eyes and ears, not the fists, of the TF.
a. Considerations. The following considerations apply to employment of the scouts.
(1) The distance scouts can operate away from the main body is restricted to the range of communications and the range of supporting indirect fire.
(2) TF scout platoons can be easily over-tasked since they have only six reconnaissance platforms with which to conduct reconnaissance.
(3) Scouts are limited in their ability to destroy or repel enemy reconnaissance units.
(4) Reconnaissance and surveillance missions are usually continuous operations that require careful planning for the employment and rest of soldiers.
(5) With only three men in each team, scout platoons are limited in their ability to conduct dismounted operations.
(6) Lack of stabilized thermal imaging optics limits night observation.
b. Types of Reconnaissance. The S2 coordinates reconnaissance requirements with the S3, who supervises the scout platoon during its operations. The platoon may report directly to the TF commander. Whether mounted or dismounted, reconnaissance requires the same preparation and stealth as any other operation. The three types of reconnaissance operations—route, zone, and area—require similar techniques, but the mission dictates the type of information required.
(1) Route Reconnaissance. A route reconnaissance obtains detailed information about specific routes. Examples include road and bridge classification, obstacles, chemical or radiological contamination, proximity of enemy, and terrain that, if occupied or controlled by the enemy, affects TF movement. The number of routes reconnoitered by the scout platoon depends on the length of the routes, the enemy situation, and the nature of the routes themselves. When enemy contact is likely or expected or when the route is long and stretches through difficult terrain, the entire scout platoon may be required for that one route. If routes are short and enemy contact is unlikely, the platoon reconnoiters as many as three routes (one for each section) but no more.
(2) Zone Reconnaissance. A zone reconnaissance involves the detailed reconnaissance of an entire zone defined by boundaries. Its purpose is to obtain detailed information on all enemy, terrain, and routes within the zone. The commander states his intent for a zone reconnaissance, which may be to determine the best routes, to move through the zone, or to locate an enemy force.
(a) The commander normally assigns a zone reconnaissance mission when the enemy situation is unclear or when he desires information on cross-country trafficability. The width of a zone that a scout platoon reconnoiters depends on the type of enemy force and terrain.
(b) The zone to be reconnoitered is defined by lateral boundaries, a line of departure, and the objective. The objective provides a termination point for the mission and might be occupied by the enemy. A phase line can also be used as a termination point.
(3) Area Reconnaissance. An area reconnaissance obtains information about a specified area such as a town, ridge, woods, or other feature critical to operations. The commander must specify exactly what to look for and why. The area to be reconnoitered is designated by a boundary line that encircles it. Area reconnaissance differs from zone reconnaissance in that the unit moves to the assigned area by the most direct route. Once in the area, the platoon reconnoiters in detail using zone reconnaissance techniques.
4-17. INTEGRATION OF BRIGADE RECONNAISSANCE TROOP AND TASK FORCE SCOUT PLATOONS
There are numerous ways the TF scout platoon and the BRT can work together to perform their reconnaissance missions.
a. In the Offense. During a brigade movement to contact, the BRT is normally forward of the TFs. During the approach to the objective phase, the BRT and TF scouts may do the following (Figure 4-6):
(1) The BRT may hand over key OP positions to TF scouts as they advance through sector.
(2) The BRT may vector the TF scouts into position and keep them informed about terrain, enemy positions, and obstacles that have already been found.
(3) TF scouts can provide overwatch for the BRT scouts moving to their next series of OPs or conducting reconnaissance of the area or zone.
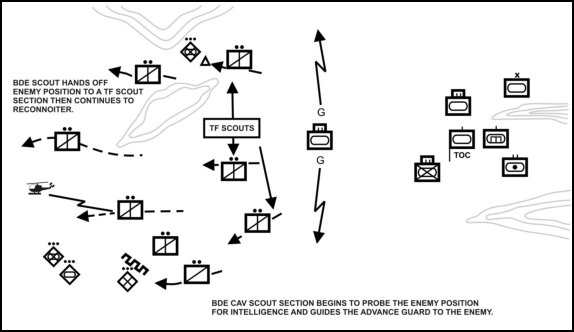
Figure 4-6. Brigade reconnaissance troop and TF scout
employment during brigade movement to contact.
b. In the Defense. In the defense, the primary mission of the scout platoon is to provide security and early warning for the task force. TF scouts may also be integrated into the brigade counterreconnaissance mission. TF and brigade scouts provide stealthy observation and early warning of the enemy's reconnaissance elements. The scout teams locate the enemy reconnaissance forces and then vector the counterreconnaissance elements to them (Figure 4-7). The scouts maintain a low signature by not engaging any targets. Tanks and Bradley fighting vehicles (BFVs) in the counterreconnaissance team kill the enemy reconnaissance. The data provided by digitization allows the scouts and counterreconnaissance team to execute a much more fluid and dynamic counterreconnaissance fight with less chance of fratricide.
(1) The employment and coordination of the TF scouts and BRT in the counterreconnaissance operation is unit- and SOP-driven. Brigade and TF scouts can be employed in depth to provide multiple screens for the counterreconnaissance force. The brigade scouts and counterreconnaissance team occupy the most forward positions. TF scouts screen behind the brigade counterreconnaissance force with each TF employing a platoon-size counterreconnaissance force to its front.
(2) Unit SOP must address procedures for inoperative scout communications systems. Scouts with inoperative systems risk fratricide; the CP should account for them by analog methods and with manual input of platforms into the informational picture. Command posts must also have some method of tracking the operational status of each scout's FBCB2 systems.
(3) In order for the TF scout platoon and BRT to work together, the TF and brigade staffs need to coordinate the following:
- Communications and digital architecture.
- Command and control architecture.
- Terrain management.
- NAI coverage and intelligence gaps.
- Fire support control measures.
- Fratricide avoidance measures.
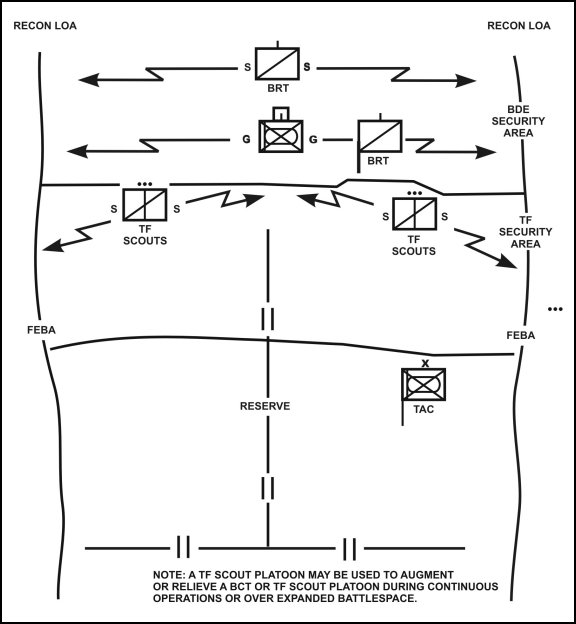
Figure 4-7. Counterreconnaissance organization of brigade
reconnaissance troop and TF scout platoon.
4-18. SUPPORTING ASSETS NORMALLY AVAILABLE TO TASK FORCE
TF commanders may have access to R&S assets from brigade and higher to include UAVs, Striker teams from the field artillery battalion, and possibly Army aviation reconnaissance assets working forward of the TF. Building the R&S plan forces consideration of maneuver, fire support, engineer placement, and C3 to link the plan seamlessly to the security force and maneuver plans. Higher headquarters normally specifies a time to forward a copy of the plan. The S2 should push the security assets out as soon as possible; the sooner the reconnaissance and surveillance assets are out looking, the more time they will have to find what the commander needs. Without a basic reconnaissance and surveillance plan, SOPs regarding default addressing, message preferences, and filter settings, reconnaissance efforts become fruitless and frustrating. The TF can use an SOP to start early reconnaissance and update the units with FRAGOs as the R&S plan is completed. Commanders specify limits of responsibility for early reconnaissance, updating them as needed.
|
NEWSLETTER
|
| Join the GlobalSecurity.org mailing list |
|
|
|

