Go to report table of contents
9.0 Security Systems Integration
9.1 The Challenge of Integration
9.1.1 Transit Security System9.2 Benefits of Integration
9.1.2 Systems Integration as an Outcome
9.1.2.1 Characteristics of an Integrated System
9.1.2.2 Measures of Integration
9.3 Transit Agency Experience with System Integration
9.4 Systems Integration Toolkit
9.4.1 The Integration Process
9.4.1.1 Defining System Scope9.4.2 Systems Engineering
9.4.1.2 Characteristics of the Integration Process
9.4.2.1 Concept of Operations9.4.3 Standards
9.4.2.2
9.4.2.2 Engineering Activity Flow
9.4.3.1 ITS Standards9.4.4 System Architecture
9.4.3.2 Other Applicable System Development Standards
9.4.3.3 Standards Development Organizations (SDOs)
9.4.4.1 Model of a System Architecture9.5 Security Integration Issues for Decision Makers
9.4.4.2 The National ITS Architecture
9.5.1 Technical Integration Issuesgo to top of the page
9.5.1.1 Design Considerations9.5.2 Institutional Integration Issues
9.5.1.2 System Architecture and Standards
9.5.1.3 Device Compatibility
9.5.1.4 Data Communications and Fusion
9.5.1.5 Integrated Legacy Systems
9.5.1.6 Security System Security
9.5.1.7 Testing and Simulation
9.5.1.8 Technology Trends
9.5.2.1 Stakeholder Involvement9.6 Systems Integration and Project Management
9.5.2.2 Interfaces with Internal and External Organizations
9.5.2.3 Inter-organizational Data Sharing
9.5.2.4 Construction and Installation
9.5.2.5 Systems Operations and Maintenance
9.6.1 Policy Formation9.7 Effective Transit Security: The Importance of Security Systems Integration
9.6.2 Capital Planning and Budgeting
9.6.3 Process Management
9.6.4 Technical Management
9.6.5 Acquisition and Supply
9.6.6 System Design
9.6.7 System Implementation
9.7.1 Transit Security
9.7.2 Systems Integration and Security
Figure 9-1. FTA Generic Security Architecture
Figure 9-2. "Vee" Model of System Development
Figure 9-3. Example of a High-Level Security System Architecture
Table 9-1. Systems Engineering Activity Flowgo to top of the page
Table 9-2. System Development Management Process Groups and the System Development Life Cycle
How is this chapter useful? For transit managers and security staff it is a resource for:
|
Enhanced security in the transit environment depends on three elements:
- Appropriate design, of the physical objects that together form the transit system, as discussed in previous chapters
- Relevant information and data, such as video images, being collected and delivered to appropriate decision makers
- Training and focus on human factors to maximize deterrence, detection, minimization, and response/recovery
Security systems integration is essential if these factors are to work together. Security systems integration implies that all types of systems and their subsystems are linked together to enhance transit system security.
This chapter defines a methodology for achieving systems integration and helping agencies meet the challenge of building integration into the systems design. The chapter reviews:
- Systems integration as an overall concept
- Systems integrations from a project perspective:
- Benefits of systems integration
- Transit agency experience with systems integration
- Methods and tools used to achieve integration
- Systems integration from the point of view of the decision maker,
- Systems integration from the point of view of the agency's system development management process,
- The importance of security systems integration
Chapter 2: A Systems Approach To Security Design, describes the need for a systems approach in designing transit security systems. This chapter defines and describes "system" in the context of the transit security system and systems integration as an outcome of the system development process and focuses on the "how-to" of systems integration.
go to top of the page9.1 The Challenge of Integration
Systems integration in the initial stages of a security systems project is a conceptual as well as a technical challenge. Key decisions relating to system boundaries, interfaces, and architecture are made early in the development process. The implications of these decisions may not be apparent until later stages of the development cycle when the system is about to be deployed.
To examine the challenge of applying the concept of integration to an actual transit security system development project, this chapter begins by defining transit security system and systems integration as an outcome.
go to top of the page9.1.1 Transit Security System
A system is a set of interrelated components that interact in an organized fashion toward a common purpose. System components may be quite diverse, including:
- Persons and organizations
- Software and data
- Equipment and hardware
- Facilities and materials
- Services and techniques1
1Adapted from: James Martin, "Systems Engineering Overview" www.incose.org/ntexas/meetings/0004what_is_se.ppt.
The function (output or product) of a system is the organizing principle that links disparate parts and determines which parts are needed, how they should be organized, and how they should be linked. |
A transit security system encompasses all physical and logical components that contribute to the safety and protection of a transit system's sites and assets. System components include physical barriers, staff credentials, electronic devices, software applications, data management, telecommunications equipment, and security personnel.
The transit security system also interfaces with other systems, such as facilities management, personnel management, and emergency services communications systems. For any security system project, the systems integration perspective can be used to evaluate how the capabilities of the security component being considered for installation relate to the capabilities of other associated elements. Agencies can then either immediately implement the link between components or defer the connection. In either case, the potential link should be recognized early in the design process and the "now or later" implementation decision should be made explicitly.
Figure 9-1 illustrates the system architecture for a generic transit security system.
 |
Figure 9-1. FTA Generic Security Architecture |
Ideally, the integrated transit security system is a real-time networked data system linking all functional elements to decision support software and/or to decision makers. If a communications and data management infrastructure is used to achieve systems integration, the integrating infrastructure itself must also be secured; and information and relevant cybersystems security included in transit security planning objectives. Dimensions of information security include such items as hardening information communications infrastructure, access control to infrastructure, protection of mass storage media, disaster recovery measures, routine back-up procedures, and continuity of operations plans and procedures.
go to top of the page9.1.2 Systems Integration as an Outcome
The outcome of systems integration for a transit agency is systems and equipment that are able to effectively intercommunicate.
Systems integration applies both to how the security system's components work together as a whole toward the intended function, and to how the security system communicates with other systems having related transit functions. Federal standards define systems integration as the "progressive linking and testing of system components to merge their functional and technical characteristics into a comprehensive, interoperable system. ... [The] integration of data systems allows data existing on disparate systems to be shared or accessed across functional or system boundaries."2
2ANS T1.523-2001, Telecom Glossary 2000 is the update and revision of FS-1037C, Telecommunications: Glossary for Telecommunications, http://www.its.bldrdoc.gov/fs-1037/.
High levels of transit security systems integration lead to timely and relevant information transfer among both security and non-security systems, and contribute to improvements in:
- Deterrence: measures that discourage a terrorist from acting
- Detection: measures that discover and identify the nature of a terrorist attack3
- Minimization: measures that mitigate against the destructive and injurious effects of an attack
- Response: measures that enable officials to counteract the terrorist attack, and to protect the public
- Recovery: measures that enable the system to resume normal operations
3The ability of integrated systems to minimize the immediate effects of an attack in progress is indirect. Most minimizing countermeasures are items like standoff zones around facilities and hardening building structures.
When looking at the outcome of systems integration; there are two important questions: "How do you know when you have reached the goal of an integrated system?" or "what are the characteristics of such a system?" and "What methods can be used to reach a high degree of systems integration?" The following subsections address these questions.
9.1.2.1 Characteristics of an Integrated System
In the same way that a system has multiple facets, systems integration occurs over spatial, temporal, institutional, functional, and data dimensions.
An integrated system has the following characteristics:
Systems integration provides networked, real-time data collection, management, and dissemination for decision support to all relevant institutional players. |
- Information generation: synthesizing data into information that can be used for decision making; for example, automatically identifying suspicious activity by flagging anomalies in a stream of visual or auditory data
- Communication: delivering the information to relevant decision makers, including external agencies and the public, where applicable
- Multiple internal and external organizations: linking multiple agencies enabling coordinated action
- Multiple devices: linking multiple devices, including single types of devices from multiple vendors and multiple types of devices; for example, an attempted unauthorized access could trigger video camera surveillance
- Multi-directionality: enabling multi-way communications among devices and control centers where needed
- Redundancy: maintaining the functionality of a security system during an attack is critical, especially if one part of the system has been disabled
- Persistence: preserving the ability to investigate past system states
9.1.2.2 Measures of Integration
Integration is more than an all-or-nothing attribute of systems. It can be present in degrees and can be implemented as part of a phased system-development process. Agencies can evaluate the degree to which integration is achieved within a system based on the following system characteristics:
Systems integration as an outcome can be recognized when the system provides timely, actionable information to organizational entities that did not have that information available prior to system implementation. |
Systems integration provides networked, real-time data collection, management, and dissemination for decision support to all relevant institutional players.
- Real-time information4
- Real-time communication
- Comprehensiveness
- Interoperability
4Most dictionary definitions regard data and information as synonyms; however, a distinction between "data" and "information" is useful and is maintained in this document. "Data" refers to a structured representation of the real world, including ideas and opinions, that is amenable to analysis by humans or by machines. Information is data that has been analyzed or further structured so that it has meaning (or semantic content) for human beings and is actionable.
go to top of the page
Real-time Information
The integrated security system will need to present data about an event from multiple sources, as close to the beginning of that event as possible. The data will need to be transmitted in a form that matches the requirements of the organization, person, or system receiving it. An integrated security system will also need to be able to archive data being collected, for later investigation and analysis. In the event of an attack or attempted attack, past data should be available to investigate possible prior probes and tests made by the attackers.
Real-Time Communication
Communications is both a means and an end of transit security systems integration. Data and information are transmitted among diverse system components to integrate the actions of those components. The communications channels used by the security system may also be used to transmit information to system staff, external agencies, and the public during an attack.
To deliver the density of real-time data needed to ensure transit security, the security system must be capable of sending large amounts of data at high speeds. This speed is determined by how long the data takes to travel across the network, and the amount of time the data may be held at the originating device and intervening nodes before being transmitted.
Comprehensiveness
Comprehensiveness refers to the full scope of a security system's capabilities. This is not evaluated as the sum of the capabilities of individual system components, but rather as how the components communicate among each other to achieve desired ends. The degree of integration present in a system depends on whether it has interfaces to systems that have related functions. If a system has no interfaces, then the information it produces cannot be leveraged to other uses.
Interoperability is: "the ability of two or more systems or components to exchange information and to use the information that has been exchanged."5 |
Interoperability
Interoperability is: "the ability of two or more systems or components to exchange information and to use the information that has been exchanged." Interoperability can be a matter of degree and of the observer's point of view. If a system can accommodate diverse devices and enable them to communicate functionally, the degree of interoperability is high.
The ability of systems to interoperate is usually dependent on the existence of and adherence to accepted, widely distributed standards, which are discussed in Section 9.4.3. A transit security example of interoperability is a video surveillance system, where the components may have been acquired from different vendors at different times, but can all be networked to a central monitoring facility.
5Institute of Electrical and Electronics Engineers. IEEE Standard Computer Dictionary: A Compilation of IEEE Standard Computer Glossaries. New York, NY: 1990.
go to top of the page
9.2 Benefits of Integration
Integration benefits result both from the avoidance of the opportunity costs of building stovepipe systems and the increased efficiency resulting from the ability of integrated systems to improve the delivery of transit services and enhance security.
Since there are few transit projects with a strong systems integration focus, there are few quantifiable measures of the benefits of integration in the transit industry. However, the experience of the aerospace industry and other industries developing large-scale integrated systems, provides some measures of the kinds of benefits for transit security.
These include:
- Reduced maintenance costs
- Integrated future system enhancements
- Enhanced cost distribution across functions
- Inter-organizational coordination
- Economies of scale
- Fast delivery of information
- Leveraged specialized expertise
- Visibility of security issues
- Continuous technology improvements
- Application to other systems
- Avoidance of installation failures
Reduced Maintenance Costs
Respondents at agencies with multiple systems performing the same function in different locations report that the costs of training personnel to maintain diverse systems exceed a desirable level. More uniformity in devices and communications architecture will ease the agency's ability to maintain the security system.
Integrated Future System Enhancements
With the development of new transit facilities, such as a new transit line, a transit property with multiple security system architectures must evaluate how each of these system architectures will be integrated with the new system. If there has been a more uniform implementation for all of the project architectures, the evaluation of integrating new systems architectures is likely to be more straightforward.
Enhanced Cost Distribution Across Functions
Security consultants and studies emphasize the benefits of multipurpose systems. One such study, completed by the National Research Council (NRC), calls for "security methods and techniques that are dual-use, adaptable, and opportunistic." These methods "mesh security with other operational tasks and objectives, such as curbing crime, dispatching and tracking vehicles, monitoring the condition of infrastructure and assuring safe operations."6 A major benefit is the ability to distribute costs among different cost centers. For example, one transit agency uses the same smart card technology for fare collection and facility access control; thus, distributing the costs of acquiring and maintaining this technology across functions.
6National Research Council, op. cit., p. 220.
Inter-organizational Coordination
From debriefings of transit and transportation agency response in New York, New Jersey, and Connecticut on September 11, 2001, it is clear that inter-organizational and interpersonal relationships developed prior to that date were instrumental to the impressive system response, even in the face of the failure of many communications channels. Early and continuing stakeholder input over many projects increases the ability of system personnel to mount a robust response to major incidents.
Economies of Scale
Related to the reduction of maintenance costs, total system development life cycle costs can be reduced by increased system integration and the replication of security system elements throughout a transit network. In the past, piecemeal solutions have been implemented by transit agencies because resources could not be obtained to acquire system-wide solutions. Nevertheless, the case can be made that the total cost of ownership of an integrated system will be less than the sum of the costs of ownership of multiple non-integrated systems.
Fast Delivery of Information
A respondent described the ideal video surveillance system as delivering images to the operations, police, and safety units. Another respondent stressed that images produced by video systems installed in transit vehicles must be viewed in real-time by the transit police, so that law enforcers can respond as quickly as possible with as much information as possible. Integrated systems have the potential to increase the ability to quickly deliver information to the parties that need it when they need it.
Leveraged Specialized Expertise
A standards-based architecture allows for upgrades using industry-wide procedures and is not dependent on the continued support of a single vendor. |
Systems integration is a function of the convergence of communications, information, and electronic technologies with transportation system elements. Specialized expertise is needed to implement these systems. Regardless of whether this expertise is in-house or outsourced, increased systems integration means that the level of expertise can be leveraged across individual projects. If heterogeneous systems are installed, the opportunity to build the expert capability can be lost.
Visibility of Security Issues
In conversations with transit officials, the perceived relevance of transit security systems for countering terrorism is low (except in the case of the largest systems in cities assumed to be terrorist targets). One respondent even called security "an afterthought." Transit agencies remain focused on everyday concerns, such as crime prevention. An integrated approach that treats security issues along with crime prevention, safety, and other concerns will help keep security on the table as a function of new access control, video surveillance, and other systems being planned.
Continuous Technology Improvements
The systems engineering approach takes into account future developments in technology, enhancing the ability to integrate future enhancements. A known architecture built of elements based on standards presents an upgrade path that is not possible with heterogeneous systems or with many proprietary systems. A standards-based architecture allows for upgrades using industry-wide procedures and is not dependent on the continued support of a single vendor.
Applications to Other Systems
The systems integration processes applied to transit security systems can be used for other transit-related systems using convergent technologies. As with other benefits of systems integration listed in this subsection, the process and technical expertise acquired by the transit agency can be applied to other agency development projects that incorporate increasing levels of digital and communications technology. A prime area of convergence are the technologies used in ITS.
Avoidance of Installation Failures
Agencies have a greater chance of avoiding system failures in implementing transit security systems, if they use the systems engineering process and focus on building systems integration into the system. For example, the defective installation of properly specified equipment can be avoided if the systems engineering process institutes quality assurance controls and if the agency recognizes that the specifications for installing the device were as important as the specifications for the device itself.
go to top of the page9.3 Transit Agency Experience with System Integration
A principal benefit of building integrated systems is institutional. Once organizations begin working together on technology-centric issues, the lines of communication begin to be created for intra-agency cooperation around other strategic and operational issues. |
Transit industry respondents report that their agencies operate with highly insular organizational structures. New projects are run from the perspective of "getting the job done at the lowest cost" and fending off interference from other agency departments. Most transit agencies make contract awards to the lowest cost bidder without a separate assessment of the technical merit of the proposal. Without close attention to the technical parameters of the procurement, the procurement method may not be adequate for evaluating issues like future expandability and interoperability.
Systems integration is seen as expensive, time consuming, and placing potential barriers in the way of completing a project. One networking official observed that although his shop had responsibility for the design and operations of the OCC, new security systems being installed were not integrated with OCC operations. Another operations executive mentioned that new train control systems were kept from the communications networking unit.
Transit professionals report that systems expertise is most available from systems service and equipment vendors. However, the vendors promote proprietary systems that are not likely to be interoperable with future systems to be installed. Transit agencies reportedly lack the detailed technical knowledge about information technology and telecommunications to write procurement specifications that hold vendors to open standards. Agencies have found that the vendors offer their proprietary systems at cheaper costs than systems with a higher capability for interoperability. One large transit agency was reported to have installed a series of proprietary access control and video surveillance systems over time, none of which interoperate with each other.
Interoperability can lead to an increased ability to use a single technology for different purposes. Examples of leveraging technological installations among various functions in a transit agency include:
- Voice and text communications between operations center and bus operators
- AVL monitoring through laptops and from police vehicles and traffic helicopters
- Linking environmental and power control systems, such as heating, ventilation and air conditioning (HVAC), to security control operations based on information about an incident
- Establishing a back up operations center with back-up power
Respondents for this study agree that transit agencies tend to be divided into silo organizations which are turf-conscious and often not overly willing to share information across organizational lines. A principal benefit of building integrated systems is institutional. Once organizations begin working together on technology-centric issues, the lines of communication begin to be created for intra-agency cooperation around other strategic and operational issues. Practiced communication will be essential in responding to a serious incident.
go to top of the pageWarning: This document contains sensitive security information controlled under the provisions of 49 CFR Part 1520
9.4 Systems Integration Toolkit
Section 9.1 describes systems integration as a desired outcome. This section describes the processes, methods, and tools that can be used to achieve systems integration, and how they lead to a definition of the security systems project that is comprehensive and holistic, and that takes into account the present and future requirements of related external systems.
The section defines and describes the following concepts:
- The integration process
- Systems engineering
- Standards
- System architecture
9.4.1 The Integration Process
Agencies should consider starting the integration process before identifying and defining a particular project. |
It is tempting to think of systems integration as assembling the subcomponents of a system or joining the system through interfaces to other systems. However, systems integration begins before the project comes into formal existence. Without the ability to integrate being designed into the system requirements, the ability to integrate the system with other systems in its environment is reduced.
This subsection outlines the steps that agencies should consider for achieving systems integration, both at the beginning and at the ending stages of the system development life cycle. These include defining system scope and characteristics of the integration process.
go to top of the page9.4.1.1 Defining System Scope
The critical step toward an integrated system is determining what to include as part of the system. It is essential to promote an inclusive perspective. Even if practical limitations restrict the scope of any final implementation, a comprehensive view should inform the planning process. Factors to consider include:
- Stakeholders
- Time horizon
- Spatial elements
- System lifecycle
Stakeholders
Identifying stakeholders and collecting their input is the first step in system definition. Depending on their roles within the security infrastructure and the transit system at large, different stakeholders may have very different perspectives on what should be included in the definition. If only a narrow set of perspectives is used to determine system boundaries, then opportunities for leveraging the system and making functional links with other systems may be missed. Relevant stakeholders may include any staff at transit agencies and other agencies working in the areas of information technology, telecommunications, ITS, transit police activity, facilities planning and construction, maintenance, and transit operations
Time Horizon
Based on past transit system experience with technology, system designers can expect that budget constraints and institutional conservatism will lead to transit security systems remaining in service for as long as practicable, despite expected lifetimes, or advances in technology. It becomes critical that agencies consider extending systems operation analysis well into the future with no limitation of existing conditions or technology.
Predictive analysis enhances the ability of the security system to adapt to changes in many factors, including:
- Size of the transit system (ridership, assets)
- Configuration of the transit system
- Transit system service demographics
- Technology (ITS, information systems, communications, security systems)
- Level of terrorist threat and public expectations of adequate threat response
Spatial Element
Any particular instance of a security installation project may not encompass an entire system, but system planners should understand how that project affects, and is affected by, the rest of the system. |
Agencies should consider inspecting the expected physical scope of the security system in tabletop exercises and on the ground in the earliest stages of system definition. System planners should be as inclusive as possible. Agencies should also consider not constraining spatial dimensions by organizational or institutional boundaries. Where a transit facility is co-located with a facility owned by another agency or company, it is critical for the security plan to indicate the existence of the adjacent facility and exploit opportunities for linking security systems where possible.
System Life cycle
Life-cycle activities, from system conception through system retirement, are usually presented in a list as if they occur linearly. In practice, these activities are often iterative, can be simultaneous, and are driven by negotiations among system stakeholders, developers, and sponsors. Agencies should consider continually revisiting system boundaries at each milestone in the lifecycle, to ensure the existing plan reflects any new information or decisions added in the course of development.
Overall, the inclusion of relevant stakeholder representatives and adopting a wide view of system boundaries will encourage the development of an integrated system. This counters the tendency to pursue stovepiped development that narrowly draws system boundaries to minimize the technological and political challenges that arise. The development of an integrated transit security system requires that, at a minimum, connectors be built among the stovepipes, but ideally that stovepipes not be built at all.
go to top of the page9.4.1.2 Characteristics of the Integration Process
Successful integration is made up of the following characteristics:
- Top-down and bottom-up
- Application of standards
- Use of systems engineering
- Construction of a systems architecture
- Layered, phased approach
Top-down and Bottom-up
Producing an integrated system should be both a top-down and bottom-up process. Top-down analysis focuses on the big picture, and is especially important in the initial planning, analysis, and design phases of development. A top-down focus promotes an integrated design that can accommodate later expansion through the addition of more device types or data types.
Bottom-up processes address the separate components, which must be integrated into a functional whole. This is particularly relevant in the last stages of the development, when the integrated system is assembled, tested, and implemented.
Application of Standards
Standards can be applied to the components that are developed, as well as to the process used to achieve integration. The use of standards to drive the process will help ensure that the activities needed to produce an integrated system are carried out and that all stakeholders are aware of the reasons for the activities. (See Section 9.4.3).
Use of Systems Engineering
This document proposes the use of the systems engineering methodology as the standard for developing an integrated transit security system. (See Section 9.4.2)
Construction of a System Architecture
Creating a security system architecture provides a context for the design of individual projects and increases the likelihood of a high degree of systems integration. The National ITS Architecture will be the framework of the system architecture, where applicable. (See Section 9.4.4)
Layered, Phased Approach
The application of a layered, phased approach to developing an integrated transit security system produces an architecture that has distinct building blocks or subsystems, and can be phased in over time.
go to top of the page9.4.2 Systems Engineering
What is Systems Engineering? The systems engineering method provides a disciplined focus on the end product, its enabling products, and its internal and external operational environment (i.e., a system view) both at the beginning and end stages of the systems project. It also provides a consistent vision of stakeholders' expectations independent of daily project demands (i.e., the system's purpose). |
Systems engineering is a methodology for achieving integration. System engineering expert James Martin describes the method as:
- An approach which views the entire system of components as an entity rather than simply an assembly of individual parts ... a component designed to work properly with other components rather than to function by itself.
- A methodology that can be applied across engineering disciplines and is now considered a discipline in and of itself.
- A way of thinking that is holistic.7
7Adapted from: James Martin, "Systems Engineering Overview" www.sjsu.edu/faculty/ekujawski/SE_briefing.ppt.
The key objectives of systems engineering do not involve building or assembling the actual system components, but instead focus on ensuring that integration is built into the system. Systems engineering objectives and activities may be considered as being "above-the-line"; having a higher-level, holistic, and integrative perspective. Designing and constructing the detailed components of a system may be thought of as lower-level or "below-the-line."
Systems engineering (or "above-the-line") objectives include:
- Goals/Concept of Operations (ConOps). Identification and quantification of system goals.
- Design and Architecture. Creation of alternative system design concepts and performance of the selected design concept.
- Integration Test: Verification that the design is actually built and properly integrated in accordance with specifications.
- Validation: Assessment of how well the system meets the goals.8
go to top of the page
9.4.2.1 Concept of Operations
To guide the process, agencies should consider developing a concept of operations (ConOps) document as a guide. The ConOps is a critical document that describes the characteristics of the to-be-delivered system from the users' viewpoint, and communicates the overall quantitative and qualitative system characteristics to the user, buyer, developer, and other organizational elements. It describes the user organization(s), mission(s), and organizational objectives from an integrated systems point of view.9 This could be an initial step to plan the introduction of a transit system credential.
9IEEE P1362, IEEE Guide for Concept of Operations Documents, Draft 3.1, 4 January 1998
The following subsections describe the systems engineering method. Section 9.4.2.1 describes the "vee" model which distinguishes systems engineering from component engineering and Section 9.4.2.2 gives a brief discussion of the activities and their products contained in the engineering activity flow. Other sections describe how development and device standards and the system architecture contribute to systems integration.
go to top of the page9.4.2.2 The "Vee" Model of System Development10
10Martin, op. cit.
A key concept in systems engineering, the "Vee" model is an approach that takes into account both a "bottom-up" and "top-down" perspective. (See Figure 9-2.) This model also illustrates the difference between systems engineering and component engineering. Note that the "above-the-line" activities match the objectives presented in Section 9.4.2.
The top-down portion of the Vee on the left of Figure 9-2 represents activities that define the system and its components in greater and greater detail, but with continual attention to the overall goal of the whole system. The bottom-up portion of the Vee on the right represents activities that build an integrated system, by assembling the lowest discrete components into modules, modules into subsystems, and so on, with continual verification that the components meet requirements of the entire system.
The vertex of the Vee represents the phase in which the component parts are built, acquired, or assembled. This approach should be applied to the whole system, as well as to each successive layer of components that make up the system. The development process is therefore a series of Vee's that are applied to each of the building blocks (and sub-building blocks), as well as to the whole.
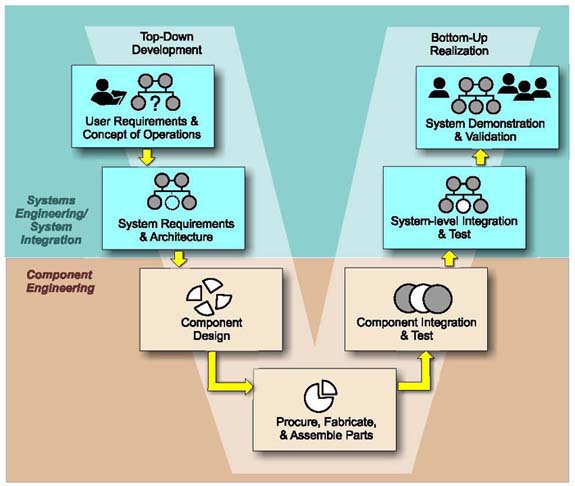 |
Figure 9-2. "Vee" Model of System Development |
9.4.2.3 Engineering Activity Flow
The systems engineering activity flow11 in Table 9-1 provides more detail on the range of activities needed to produce an integrated system. The table lists the questions and sample outcomes from each activity that should be answered at each flow step. The last column relates the activity to the systems engineering objectives listed in Section 9.4.2 and the "Vee" model of system development in Figure 9-2.
11Adapted from Martin, op. cit.
Table 9-1. Systems Engineering Activity Flow
| Engineering Activity | Example Questions Posed in Step | Examples of Step Outcomes | System (S) or Component (C) Engineering Activity |
|---|---|---|---|
| Need | What needs are we trying to fill? What is wrong with the current situation? Is the need clearly articulated? |
Project Charter System Acquisition Documents |
S (Goals/ConOps) |
| Operational Concept | Who are the intended users? How will they use our products? How is this different from the present? |
Concept of Operations | S (Goals/ConOps) |
| Functional Requirements | What specific capability will we provide? To what level of detail? Are element interfaces well defined? |
User Requirements | S (Goals/ConOps) |
| System Architecture | What alternative designs exist to fulfill user requirements? What criteria will be used to choose among the alternatives?What is the overall plan of action? What elements make up the overall approach?Are these complete, logical, and consistent? |
System Design | S (Design and Architecture) |
| Allocated Requirements | Which elements address which requirements? Is the allocation appropriate? Are there any unnecessary requirements? |
Technical Requirements | S (Design and Architecture) |
| * Detailed Design | Are the details correct? Do they meet the requirements? Are the interfaces satisfied? |
Sub-System/Component Specifications | C |
| * Implementation | Will the solution be satisfactory in terms of cost and schedule? Can we reuse existing pieces? |
Sub-system/Component Construction/Acquisition | C |
| Test and Verification | Has the as-built system met specifications? Do components function as a whole according to the design? |
Test ResultsIntegrated System | S Integration Test |
| Validation | Does the system meet customer goals? Does the customer accept the system? |
Acceptance Test Results Deployed System |
S Validation |
Note:
* Shaded (marked with asterick) rows denote component engineering "below-the-line" activities.
Unshaded (non-marked) rows denote systems engineering "above-the-line" activities.
9.4.3 Standards
Standards and System Integration The use of standards can contribute to systems integration by increasing the likelihood that the subsystems or modules can be assembled into an integrated system without further rework and that the system will be able to link with related systems. |
Standards reflect agreements on products, practices, or operations by nationally or internationally recognized industrial, professional, trade associations, or governmental bodies.12 The use of standards can contribute to systems integration by increasing the likelihood that the subsystems or modules can be assembled into an integrated system without further rework and that the system will be able to link with related systems.
Standards can apply not only to hardware, data formats, and communications protocols, but to the systems-development process and other processes, such as risk management and quality assurance. System development standards can increase the likelihood that a developed system will show a high and functional level of systems integration.
12 From Federal Standard 1037C. See http://glossary.its.bldrdoc.gov/fs-1037/dir-034/_5071.htm.
While the use of standards may be a necessary precondition for systems integration, they are not sufficient. There are typically multiple standards for any field, and the choice of standards can be confusing given the profusion of organizations managing the development and publication of standards, namely the standards development organizations (SDOs), national versus international standards, standards that cross engineering disciplines, and evolving standards that are in a continual cycle of playing catch-up with advanced digital and telecommunications technologies.
A key to selecting standards is to determine which existing published and unpublished standards are the actual, current, de facto standards in the transit operations and transit security communities. This is best accomplished by peer-to-peer communication.
Examples of relevant standards and associations for systems integration include ITS standards, other applicable systems development standards, and SDOs.
go to top of the page9.4.3.1 ITS Standards
ITS applies digital, communications, and electronic technologies to transportation operations. To accelerate the deployment of ITS technologies, the U.S. Department of Transportation has sponsored the development of a series of standards that are applicable to ITS projects. These standards address the full range of system components, including communications protocols, communications interfaces, data dictionaries, and message sets. They are based on open technologies and are meant to reduce reliance on proprietary systems.
The Transit Communications Interface Protocols (TCIP) are ITS standards that address the data communications requirements for public transportation, including the exchange of information among public transit vehicles, transit operations centers, external agency operations centers, and other transit facilities. These standards are being used in field operational tests.
go to top of the page9.4.3.2 Other Applicable System Development Standards
Achieving systems integration depends on communication, either as part of the system being implemented or as a means to determining how all system elements (such as mechanical or electromechanical devices) should be integrated.
Examples of standards related to the process of system development include:
- EIA 632, Processes for Engineering a System: This standard, based on a compilation of best practices already in use, defines what the processes are and what their results should be, but it does not define how the processes are accomplished or what tools should be used.13 The approach for transit security systems integration in this document is based on EIA-632.
- ISO/IEC 15026, System and Software Integrity Levels Managing Risk: This standard focuses on system risk assessment and mitigation. It assigns an integrity level (performance reliability) to each functional component of the system, and uses these integrity levels to evaluate the overall system.14
13For additional information, see ANSI/EIA-632-1998.
14For additional information, see ISO/IEC 15026, International Standard - System and Software Integrity Levels, as quoted by "FAA Safety and Security Practices - Call for review".
http://www.faa.gov/ipg/pif/evol/IntegrityAssuranceReviewPackage-18Nov.pdf.
go to top of the page
9.4.3.3 Standards Development Organizations (SDOs)
SDOs that are active in areas relating to transit security systems integration are a helpful resource for selecting and establishing standards.
Relevant SDOs include:
- American National Standards Institute (ANSI)
- American Public Transportation Association (APTA)
- American Society for Testing and Materials (ASTM) formerly, now ASTM International
- Electronic Industries Alliance (EIA)
- International Electrotechnical Commission (IEC)
- Institute of Electrical and Electronics Engineers (IEEE)
- Internet Engineering Task Force (IETF)
- International Organization for Standardization (ISO)
- Institute of Transportation Engineers (ITE)
- National Electrical Manufacturers Association (NEMA)
- National Transportation Communications for ITS Protocol (NTCIP)
- Society of Automotive Engineers (SAE)
9.4.4 System Architecture
System architecture s an intermediate step in the system development life cycle between requirements specifications and the detailed design of system components. Using an object-oriented perspective,15 the system architecture identifies the basic uses of the system, allocates those uses among active objects, and allocates the objects among the hardware, communications, and software components of the system. The architecture identifies system components to be developed in the immediate project, as well as those that will be part of future system development phases.
15Object-oriented systems analysis refers to associating functions and data in objects, which can be related to each other, for example, in classes where objects that belong to a class can inherit characteristics from the object that defines the class.
go to top of the page
9.4.4.1 Model of a System Architecture
The system architecture provides a blueprint of the system's components and how they fit together. It is essential to achieving a high degree of systems integration for any system development effort.
The system architecture identifies:
- Security devices, such as CCTV
- Production and (if different) development hardware/operating systems
- Major software objects or components-both process and data-and their interactions
- How the technical architecture will link the components into a whole
- Standards to be used in the implementation
Figure 9-3 is a high-level model of a system architecture, illustrating the types of entities that an actual system architecture would describe in detail. The National ITS Architecture is presented as the overarching framework under which a transit security system is likely to be designed.
 |
Figure 9-3. Example of a High-Level Security System Architecture |
9.4.4.2 The National ITS Architecture
The National ITS Architecture defines the physical entities or subsystems, the data flows among them, and the functions that govern those flows. The overarching national architecture provides the framework for a regional architecture, which in turn provides the framework for the architecture of implemented local systems. One of the 31 user services defined by the National ITS Architecture is Public Travel Security, which defines the information flows "to create an environment of safety in public transportation."16
16National ITS Architecture 5.0. See http://itsarch.iteris.com/itsarch/html/user/usr24.htm.
Agencies can decide which standards to use when they determine the system architecture. The use of ITS standards may be required by the FTA, depending on the development status of the particular standard, and the use of some ITS standards will have already been incorporated into the regional ITS architecture. Note that the FTA requires its grantees to use the National ITS Architecture and the relevant regional architectures for projects such as security systems.17 There are opportunities to leverage security applications with ITS applications, and take advantage of ITS standards, especially in communications. For information on ITS standards refer to http://www.its.dot.gov/arch/arch.htm and http://www.standards.its.dot.gov.
17FTA Master Agreement,http://www.fta.dot.gov/library/legal/agreements/2004/ma.html.
go to top of the page
9.5 Security Integration Issues for Decision Makers
Many transit information technology and security professionals recognize the benefits of security systems integration. However, given the transit system planning and procurement environment of slow technological change, long capital depreciation horizons, and well-understood requirements, security systems, which include devices based on rapidly changing information and communications technologies, pose a challenge.
To the extent that transit systems focus on security concerns, they mostly plan for a response during and after the event. Recognizing the need to provide help regarding security threats and vulnerabilities, the FTA is providing multi-disciplinary technical assistance teams to the 50 largest transit agencies.18 The result is that the transit industry is now identifying critical assets and methods to harden their systems.
Measures related to pre-event prevention, detection, and deterrence tend to be considered when new facilities are being planned, designed, and constructed. Transit professionals recommended the following overall strategies for developing integrated transit security systems:
- Implement and evaluate pilot projects as part of a comprehensive plan that enables the transit agency to avoid a proliferation of pilots and a low level of integration
- Use proven, widely deployed, commercial-off-the-shelf solutions
- Test and retest systems for robustness in 24/7 operations for the desired level of integration Secure the communications system with layers of security that employ both authentication and encryption
18For further information, see http://transit-safety.volpe.dot.gov/Security/Default.asp
Transit agencies should consider addressing issues relating to the degree of transit security system integration. These issues are based on systems engineering literature and the experiences of transit agencies and are classified into technical integration issues and institutional integration issues.
go to top of the page9.5.1 Technical Integration Issues
Budget constraints are a reality and require tough decisions with resource allocation. The following technical issues are considered the most important for agencies to address to enhance system integration when developing a transit security system.
Design considerations- System architecture and standards
- Device compatibility
- Data communication and fusion
- Integrated legacy systems
- Security system security
- Testing and simulation
- Technology trends
These issues assume that the agency is following the systems engineering process outlined in Section 9.4.2, in particular the production of a concept of operations document.
go to top of the page9.5.1.1 Design Considerations
Agencies should consider investing adequate resources in the planning, requirements definition, and design stages of a systems integration project. One author referring to information systems development, reports that "[I]nsufficient investment in the early design phases (5 to15 percent) is likely to lead to project cost overruns [sic] of between 50 and 100 percent for both hardware and software projects."19
The budget constraints faced by transit agencies may lead to reducing funds, time, and personnel dedicated to the initial project stages. However, especially for projects introducing new technologies and for projects integrating new and legacy technologies, it is critical for system planners and developers to reserve adequate resources for initial project stages.
One respondent, a security consultant, observed that transit agency personnel face time pressures that hinder their ability to learn enough about the capabilities of new technologies to frame clear requirements. Transit agency personnel should consider creating the policies and procedures for using the information that is being generated by the integrated security system.
In addition, there are institutional pressures for early, concrete project results. These may lead to premature system development and failures, like the inadequate installation of security system devices at one transit system.
Recommendations for enhancing security systems integration include:
- Use tests, simulations, and table top exercises to determine the requirements for the system during the initial stages of the development life cycle (not just at the end)
- Increase spending on the initial stages of the life cycle when the project contains new technology and new capabilities outside the experience of the transit agency
- For the largest systems, consider creating a special-purpose security operations unit within the OCC, with the requirement that the unit be physically and technologically able to communicate freely with other OCC staff
- Create the design in layers, including layers of deterrence, detection, and response, and layers to protect the security system itself
- Generate well-formed system requirements, including data sources, data stores, information users, and operational procedures
- Visit transit agencies of similar scale and network characteristics that have installed security systems, when possible, and evaluate the extent of integration in evidence for those systems.
9.5.1.2 System Architecture and Standards
Most respondents favored the use of an architecture based on standards, rather than one based on a proprietary system. At the same time, most respondents acknowledged that existing transit security systems were constructed around proprietary systems, either because the legacy systems predated relevant standards or because the proprietary system was seen as the least costly option.
New systems development presents more of an opportunity to implement standards. The practitioners cited ITS standards as well as the communications and information technology standards used across economic sectors that have been developed by standards development organizations, such as the Institute of Electrical and Electronics Engineers (IEEE). One practitioner found ITS standards useful in the new system context, because they improved the ability to link the system with ITS functions.
In each of the system component types indicated in Figure 9-1, the agency system developer should consider whether or not to use newer technologies. Different transit systems are likely to reach different conclusions on the use of cutting-edge technology and devices. The choice will depend on the organization's tolerance for risk, comfort with innovation, and willingness to predict the likely direction of technology in the future. Trailing-edge technologies may be proven, and reliable, but may face obsolescence and be unable to interface with newer technologies in a relatively short time frame.
go to top of the page9.5.1.3 Device Compatibility
A fundamental decision for systems integration is determining which components (human or electronic) need to communicate with each other. This decision needs to be made for both devices with the same function as well as devices with differing functions.
Agencies must carefully specify the parameters that determine the interchangeability and interoperability of security devices to ensure that functional compatibility will exist. Practitioners recommend using a disinterested expert to develop specifications for the devices, such as university researchers, although this group is likely to be biased in favor of new technologies.
go to top of the page9.5.1.4 Data Communications and Fusion
Importance of Defining Data Subtle differences that exist in data definitions between agencies may make the exchanged data misleading and, perhaps, unusable. |
Data integration is essential to the achievement of an integrated system. When integrating diverse system architectures, especially when creating interfaces to external agency systems, data fusion (or combining data stored or generated by diverse systems) can be a complex, costly, and risk-filled exercise.
Data communications are usually modeled as a stack of interacting layers from the link's physical characteristics (e.g., the type of wire) at the lowest level, to the data's semantic content at the highest level. The key to data integration is the use of standards and careful accounting for any deviations from the standards chosen.
go to top of the page9.5.1.5 Integrated Legacy Systems
Given the fiscal constraints faced by most transit systems, it is expected that integrating new technologies into legacy systems will be a constant feature of security systems development. One large transit system currently uses surveillance video systems to determine the state of system operations, such as train location and the density of crowds on station platforms. The transit agency is now considering enhancing these systems for use in video surveillance for crime prevention and for countering terrorism.
Integration issues to be evaluated include:
- The remaining useful life of the equipment
- Camera placement
- Enabling video feeds to the security operations center
- Installation of a SCADA system for the video equipment; the downtime of a camera used for operational purposes is not as critical as the downtime for a security system, since the disabling of the system may mark the onset of a security incident.
Comprehensive legacy system documentation will support the integration process, including original vendor manuals, records of the installation process, and records of all changes made to the system. Agencies should consider linking to the legacy system through an interface, rather than through extensive changes to the architectures of either the legacy or the new system.
go to top of the page9.5.1.6 Security System Security
Transit agencies are already aware of the necessity for securing the security system against inadvertent or willful damage. Transit agency respondents using wireless information technology for operations stressed the importance of paying attention to the details of cybersecurity.
A strong case can be made for over-engineering the security of security systems, particularly for vulnerable, high-visibility targets, and as an insurance against known and unknown future threats. For each system, security officials should conduct security audits and establish policies that address the following:
- Device hardening against tampering and vandalism
- Device positioning (including concealment) to prevent tampering and vandalism
- Cybersecurity, for wireline and wireless networks; including firewalls
- Access control for the OCC, Network Operations Center, and/or Security Operations Center
- Protection of the transmission channel
- Protection of power sources
- Visual inspections of devices, and fixed and rolling assets
- Securing handheld and portable equipment by personnel training and strong password policies
- Encryption and authentication of data communications
- Installation of a SCADA system to monitor security system elements, power, and environmental control devices
9.5.1.7 Testing and Simulation
Importance of Testing in the System Development Lifecycle Transit security professionals stressed the necessity for testing throughout the development life cycle when asked how it was possible to determine the degree to which a security system was integrated. |
Testing is a line item that may be negatively impacted by budget constraints, but due to the failsafe nature of security systems, a robust test program is essential. Contracts with system vendors must specify that the contractor adhere to development and quality assurance standards that require life-cycle testing.
Testing begins during the initial stages of the project. Simulations, through table-top exercises that involve all stakeholders, can identify the functions and boundaries of the system and its requirements for interfaces with external systems. Pilot tests, demonstrations, and operational tests are most important for technologies that are new to the transit agency installing the security system, but are useful at any time new equipment is being acquired. In the most vulnerable segments of the largest transit systems, computer models of the transit properties being protected will be useful in designing the security system.
go to top of the page9.5.1.8 Technology Trends
Technological change is constant and fast. Moore's Law20 states that the capacity of integrated circuit chips will double every 18 to 24 months. This exponential growth has been roughly maintained since 1965. Security system planners need to be aware of both near- and long-term changes on or just over the horizon.
Security systems are beginning to use the following technologies:21
- Ubiquitous Computing. Intelligence is being incorporated into all kinds of everyday objects and appliances. With cheap, powerful, and embedded processors, security systems functionality is likely to be "built in" to fixed and rolling assets acquired by transit systems.
- Networked Sensors. Sensors will allow detection not only of chemical, biological, and radiological agents, but also (privacy concerns notwithstanding) of individuals as they traverse a space.
- Wireless Connectivity. Wireless communications can be combined with ever-present computing and networked sensors to build an intelligent sensor net that continuously monitors a vehicle or a spatial area.
- Autonomous Applications. Video applications are being developed that no longer require security personnel to monitor video images in real time; these applications include facial recognition and detection of unusual events (such as placement of a suspicious parcel on a station platform).
- Global Positioning. GPS will be applied to all vehicles and many individuals; combining GPS with wireless technology and network connectivity will extend GPS capability to enclosed spaces.
20Attributed to Gordon Moore, co-founder of Intel.
21James A. Lewis, "Security and Surveillance," Center for Strategic and International Studies, June 2002. http://inet2002.org/CD-ROM/lu65rw2n/papers/g10-b.pdf.
go to top of the page
9.5.2 Institutional Integration Issues
Transit agency respondents commented on the extent to which the individual units of their organizations operate independently. They acknowledge that a high degree of systems integration cannot be achieved without paying attention to issues of institutional integration, and recounted instances in which critical departments were either not included in the planning for security systems, or did not wish to be included. The effectiveness of the technology depends on the effectiveness of the institutional and procedural policies that govern how the technology is used.
Issues include:
- Stakeholder involvement
- Interfaces with internal/external organizations
- Inter-organizational data sharing
- Construction and installation
- Systems operation and maintenance
9.5.2.1 Stakeholder Involvement
As described in Section 9.4.1, gathering all of the stakeholders together at the outset of system planning and throughout the development process is a critical step. Budget considerations and personnel time constraints may discourage full stakeholder participation. One strategy used in a transit agency was to use a third party to help bring all relevant stakeholders together. Ideally, that organization or person should have links to all of the potential participants.
go to top of the page9.5.2.2 Interfaces with Internal and External Organizations
Routine inter-organizational contact can foster special-purpose communication. One agency respondent stressed that transportation department personnel participate in regular meetings with emergency services agencies to share criminal and incident data. As mentioned in Section 9.2, existing regular interaction among transportation and public safety agencies in the tri-state area led to a remarkably effective response by transportation personnel on September 11, 2001, even though the situation was chaotic and expected communications channels were not necessarily operational.
go to top of the page9.5.2.3 Inter-organizational Data Sharing
The amount of useful data shared among organizations is a useful measure of the degree of systems integration. Data sharing is what holds the integrated system together. However, the characteristics of the data to be shared may not be the same in every organization. In a transit example mentioned previously, video surveillance cameras provide data to the agency's safety, operations, and police units. Different agency departments have varying requirements for the timeliness of the video data. For example, the safety department may not require a continuous stream of video images, whereas security functions do.
The installation of a security system with the capability for data sharing among departments may encourage future data sharing. In one example, a transit communications manager responsible for the OCC predicted that the security department's new intrusion-detection system would be monitored centrally, rather than at a special purpose facility.
go to top of the page9.5.2.4 Construction and Installation
Coordination with the agency's construction department and maintenance of quality control throughout the installation process are critical to the success of the transit security project. The construction department is most concerned with completing its job as quickly as possible. This means department managers may not want to take the time to attend stakeholder meetings. One transit system was reported to have had a well-specified security system, but defects in the quality of the installation resulted in the communications channel being too noisy to be useful. Quality control throughout the process, as well as tight technical specifications, should help prevent a negative result.
To prevent tampering, project managers should also consider preparing security plans during construction and installation of the security system. Securing construction sites in general against crime, vandalism, and terrorist acts can help raise the security image of the transit network as a whole.
go to top of the page9.5.2.5 Systems Operations and Maintenance
A security system is only as good as the supporting training, personnel, policies and procedures. For example, in an access control system security goals may not be met if the database of currently employed personnel and their access privileges are not kept up-to-date with actual personnel events, such as terminations or promotions. Video images can go unmonitored and alarms unanswered. Data may be undigested, if the data have not been transformed into information that can be used for decision-support.
Although respondents stressed that transit operations personnel are not law enforcers, the National Research Council makes the point that the presence of transit operations personnel in transit systems make them deterrents and the true first responders with respect to terrorist attacks.22 An integrated approach requires these personnel to receive extensive training on responding to alarms generated by automated systems or on making alarms through security systems.23
Transit facilities maintenance and systems maintenance operations should consider incorporating correct procedures for new equipment in their existing work packages. Maintenance personnel can be trained to inspect new equipment and to ensure that standard maintenance procedures pose no danger of damaging the equipment.
22National Research Council, Making the Nation Safer: The Role of Science and Technology in Countering Terrorism. (Washington, D. C.: The National Academies Press, 2002).
23The American Public Transit Association (APTA) surveyed transit systems to determine their security needs. Among the most important operating needs reported by transit agencies were: training for security personnel including preparatory drills, security training for other personnel, joint transit/law enforcement training including preparatory drills. APTA, "Survey of United States Transit System Security Needs and Funding Priorities, Summary of Findings" April 2004.
go to top of the page
9.6 Systems Integration and Project Management
The system engineering activity flow in Section 9.4.2 describes the milestones reached and the results produced as a project proceeds through beginning, middle, and end. Agencies know that no project exists in a vacuum. Processes occur before the "beginning" to define and fund a project, and processes occur after the "end" to deploy, operate, and maintain the final product.
This section looks at agency decisions relating to the overall project management capabilities of a transit agency, especially "high tech" security system projects. The section gives an institutional and methodological context to Section 9.5, which presented technical and institutional factors a decision-maker should consider in relation to a particular project. Included in this section are strategies for maximizing a transit agency's ability to deploy integrated systems by creating a robust set of system development management processes. These include all processes needed for the system engineering activity flow (or system development life cycle) discussed in Section 9.4.2.2 to produce intermediate and final products.
go to top of the pageSystem Development Management Processes
System development management processes include activities that are needed not only to develop a particular system, but also include activities to create consistent processes and procedures that can be re-used for any project. Every transit agency has a unique combination of needs and resources; some considerations listed here may be more applicable to some agencies than to others; each transit agency should determine which actions best meet its goals. To reach a high level of systems integration an agency should evaluate its size, staffing profiles, and management style, among other factors, to optimize the processes to its particular situation.
The considerations present general approaches to managing system development, but each agency must identify its particular security needs to determine which approaches are appropriate. |
These are the actual processes that must be in place and executed in order to achieve the milestones, deliverables and results needed at each step of the system engineering activity flow for a particular development project. The system development management process groups include policy formation, capital budgeting and planning, process management, technical management, and acquisition and supply. Table 9-1 aligns these groups with the system engineering and system development life-cycle steps given elsewhere in this chapter.
System development management processes also include non-technical process groups, such as policy formation and capital budgeting. Integration issues are critical at these non-technical stages, because projects and their attendant constraints are typically defined as a result of these processes.
The considerations listed in the balance of this chapter summarize points made throughout this document and arrange the considerations by system development life cycle process group. Each agency must identify its particular security needs and determine which of these considerations are appropriate. They should, when consulting these considerations, consider the differences in threat levels and particular circumstances will differ among various geographic areas or facilities.
Table 9-2. System Development Management Process Groups and the System Development Life Cycle
| Process Groups | EIA 632 | "Vee" Model | System Engineering Activity Flow | PMBOK 24 :Processes | ||||
|---|---|---|---|---|---|---|---|---|
| Initiate | Plan | Control | Execute | Close | ||||
| * Policy Formation | ||||||||
| * Capital Budgeting and Planning | ||||||||
| ** Process Management | Technical Management Planning Assessment Control |
x | x | x | x | x | ||
| ** Technical Management | Technical EvaluationSystems AnalysisRequirements ValidationSystems Verification | Validation | Verification Validation |
x | x | x | ||
| Acquisition and Supply | Acquisition and Supply Supply Acquisition |
Procure Parts | x | |||||
| System Design | System Design Requirements Definition Solution Definition |
User Requirements & Concept of Operations System Requirements & Architecture Component Design |
Need Operational Concept Functional Requirements System Architecture Allocated Requirements Detailed Design |
x | x | |||
| System Implementation | Product Realization Implementation Transition to Use |
[Procure,] Fabricate, & Assemble Parts Component Integration & Test System-level Integration & Test System Demonstration & [Validation] |
Implementation Test [& Verification] [Validation] |
x | x | x | ||
Note:
* Light-shaded (marked with 1 asterick) processes are project precursors. These processes set up the policy and fiscal framework needed to begin a project.
** Dark-shaded (marked with 2 astericks) processes are supporting or methodological processes that are used to produce results at all stages of the system development life cycle.
Brackets indicate the [sub]process is included in another, more appropriate process group.
24 A Guide to the Project Management Body of Knowledge (ANSI:/PMI 99-001-2000), Project Management Institute, p.38
The system development management process groups described include:
- Policy formation
- Capital planning and budgeting
- Process management
- Technical management
- Acquisition and supply
- System design
- System implementation
9.6.1 Policy Formation
A policy represents a set of generalized principles that an organization uses to make decisions in specific instances to which the policy applies. With respect to the system development management processes discussed in this section, policy formation refers to the processes that an organization uses to decide which policies need to be created and which principles should be included within the needed policies.
The following considerations suggest ways in which a transit agency's policy formation agenda can be shaped by security systems integration concerns:
- Assigning responsibility for counter-terrorist security systems.
- Including security on every agency agenda.
- Creating in-house knowledge of technology.
Assign Clear Responsibility for Counter-Terrorist Security Systems
A transit agency should designate an organizational unit and a person within that unit to be in charge of security systems to counter terrorist activity and establish lines of authority and communication.
Even though transit operators have established or begun to establish organizational structures relating to emergency management and incident response, the responsible organizations for responding to a terrorist incident may not be the same as those charged with building security systems.
Including Security on Every Agency Agenda
An assessment of relevant security concerns should be a major component of all policy setting activities in the agency, even if the transit agency has determined that the risk to its riders, staff, and facilities from terrorist activity is low. With security always on the agenda, once a particular security systems project is underway, internal stakeholders will have a pre-existing foundation for substantive interaction around security-related issues and for ultimately reaching an integrated result.
Create In-House, Non-Specialized Knowledge of Technology and its Capabilities
The diverse functional capabilities of technology and the speed of technological change can leave non-specialists unaware of the wide range of available options. Creating non-specialized technical knowledge in-house will help system planners make the budget case for technology-based security, ITS, operations, and crime-prevention projects; acquire third-party consultants for generating usable system requirements; and prepare procurement specifications.
Even though agencies often disagree on the level of in-house technical expertise required, most practitioners recognize the need to have a clear understanding of the language and broad issues related to a particular technology.
go to top of the page9.6.2 Capital Planning and Budgeting
Transit agencies understand their capital planning and budgeting processes in relation to vehicles, facilities, and infrastructure. However, applying these processes to the acquisition of the equipment and services to produce an integrated high technology solution for transit security can present an added measure of complexity and uncertainty to the financial process group.
The budgeting process is an implicit project prioritization process that identifies which efforts must be started first. The following considerations suggest ways in which a transit agency's capital planning and budgeting can be shaped by security systems integration concerns. They include:
- Allocating resources for activities promoting integration
- Applying long-range planning processes
- Prioritizing security systems projects
Allocate Sufficient Resources for Activities Promoting Integration
A common complaint in systems development, especially in the public sector, is that budgets are not large enough to perform the job correctly. Project managers should prepare arguments for systems integration and for the activities needed to promote integration, such as stakeholder input to requirements determination and design, early testing, pilot programs, and demonstrations.
Apply Existing Long Range Planning Processes to Security Systems.
Transit agencies are experienced in long-term capital planning and budgeting and can apply these skills to security systems planning. However, security systems technology is constantly changing with more capability and functionality becoming available over time. Practitioners report that these technologies can be expected to become obsolete in a five-to ten-year period. Agencies should take upgrade paths into account in their long-range planning cycles.
Prioritize and Focus Security Systems Projects
The capital planning and budgeting process determines the size and nature of new investments in transportation assets. By definition this process sets priorities among competing program demands for funds. Prioritizing and focusing transportation security projects will require system planners to identify clear benefits and justifications when deploying a particular system.
go to top of the page9.6.3 Process Management
System development managers create a framework within which every individual project is developed. The process management process group focuses on creating tools and executing the processes to plan, assess, and control development projects.
Strategies include:
- hiring consultants to coordinate stakeholders
- using system engineering methods
- training staff continuously
Hire a Third-Party Consultant to Coordinate Agency Stakeholders
Organizational units within an agency may need an outside party to bring them all together to define the process, identify integration opportunities and technologies, and minimize stovepiped behaviors.
Use Systems Engineering Methods (EIA 632)
Applying these method, which incorporate risk assessment and risk modeling, will facilitate increased systems integration and provide a holistic point of view that promotes systems integration.
Train Staff Continuously
Ultimately, agency staff must respond to information gathered and distributed by the integrated security system. For the response to be effective and appropriate, continuous training is necessary for all affected personnel.
go to top of the page9.6.4 Technical Management
Technical management is a process group that creates and deploys the methodologies and underlying techniques for system analysis and validation. A foundation of sound methodologies will improve the transit agency's ability to implement an integrated transit security system.
Strategies include:
- Implementing a test program
- Using a phased implementation approach
- Using standards
Implement a Strong Test Program
Testing is considered a means of determining whether a system has achieved a sufficient level of integration. Testing should take place at all stages of the development life cycle and include:
- Modeling and simulation-including rehearsals, table top exercises, and systems analysis at all life cycle stages
- Validation and verification
- Operational testing
Use a Phased Implementation Approach
Transit agencies already have experience in implementing pilot projects that test a new device or method in a portion of the transit system, e.g., a new fare collection system, before full implementation. Transit agencies should consider leveraging this experience for the implementation of new security system technologies. It is equally important for transit systems to consider pilot projects as defined within a comprehensive multi-year plan to help avoid the proliferation of stand-alone pilots and ensure that the pilot can be integrated into a full system in the future.
Use Standards
Transit security system planners should evaluate standards relating to process, information technology, and communications for use in the security program. Using standards will increase the likelihood of higher levels of integration, not only for the current project but in future phases.
go to top of the page9.6.5 Acquisition and Supply
Any product, whether final or intermediate, has an acquirer; an organization that orders and receives the product, and a supplier, which creates or transfers the product to the acquirer. The product's supplier may be internal or external to the transit agency. Even for internal transactions, well-defined agreements between acquirers and suppliers are needed. Since a critical relationship is the contracting relationship, agencies should consider the following strategies when forming partnerships with contractors:
- Writing well-specified procurement documents
- Finding the "right" partner
- Using third party experts
Write Well-Specified Procurement Documents
Transit agency personnel experienced in system development, networking, and communications warn that procurement documents are being written by non-specialists, who may not be aware of all the elements necessary to ensure that the acquisition has the desired result. In particular, the "low bid" environment can have adverse affects if the procurement does not specify the desired quality and functions of the service or device.
Attention to detail in the procurement process is critical, from the acquisition of initial consultant services through the procurement of security system devices. Peer transit agencies can provide advice based on their experiences with hiring consultants, with system development and integration services, and with selecting system hardware and software.
Importance of expertise in procurements Procurement documents are being written by non-specialists, who may not be aware of all the elements necessary to ensure that the acquisition has the desired result. |
Search for the "Right" Partners
Agencies dependent on contractors may try to maintain relationships with trusted partners. However, one researcher reporting on large, complex technical projects recommends that agencies "[s]elect partners or subcontractors with a sound enterprise environment honed on projects of a similar scale and complexity. This may sound obvious but failure to heed this advice has been the cause of many project failures."25
25Stephen C. Cook, "What the Lessons Learned from Large, Complex, Technical Projects Tell Us about the Art of Systems Engineering" in Proceedings and Oral Presentation of the INCOSE 2000 Conference, Systems Engineering: A Decade of Progress and A New Century of Opportunity, Minneapolis, Minnesota, USA, 16-20 July 2000, pp. 723-730; http://www.unisa.edu.au/seec/pubs/00papers/cook-lessons.pdf.
Use Third-Party Experts
Agencies should evaluate using third-party disinterested experts, such as university research centers, rather than vendor experts, to evaluate the potential devices, architectures, and technical approaches that are available, since technology vendors are not likely to provide truly unbiased evaluations of other approaches.
go to top of the page9.6.6 System Design
The system design process group includes all processes at the beginning of the system development life cycle, from the concept of operations and requirements through detailed component design. Creating the system architecture is a key step in this process group, as it shows the connections among the various sub-systems that form the overall system.
Processes include:
- Generating system requirements
- Using COTS
- Installing the appropriate kernel
- Layering security
- Securing digital networks
- Maximizing system robustness
Generate Well-Formed System Requirements
To develop an integrated system, developers need to know who requires what information, when, and for what purpose. |
To develop an integrated system, developers need to know who requires what information, when, and for what purpose. Generating well-formed system requirements is critical for developing the core and ancillary functions for a particular security system. An excellent tactic for developing requirements is to examine how solutions were developed at other transit agencies, and the range of pre- and post-system development requirements. The transit agency cannot leave this exercise to its consultants, system developers, or integrators, because as the ultimate customer the agency must define the scope of the desired system at the outset to ensure that its needs are met.
Use Proven Commercial Off-The-Shelf (COTS) Solutions
Technology specialists contributing to this document advise agencies to avoid proprietary solutions and to use solutions based on open architectures. COTS equipment can result in cost savings since equipment that is widely used in other industries has a proven track record. However, the system planner must verify that the COTS solution is based on open architectures (or at least architectures widely supported by many vendors) and provides an upgrade path as the technology incorporates new features over time. Transit security system planners recommend expediting the procurement process to prevent the acquisition of obsolete systems and requiring the vendor to provide product support for a specified minimum period of time.
Install the Appropriate Kernel
The kernel, or core function, is the minimum set of security applications that can make up the initial phase of an integrated transit security system installation. Installing the appropriate kernel of an integrated security system in part of the agency's facilities will depend on the service characteristics of the transit system.
Consider the following two examples of the minimum technical applications needed for new tunnel construction and for bus transit.
Example. Core functions that are being implemented in new tunnel construction for one transit agency include:- Access control to rooms inside tunnels with data on usage and alarms transmitted to and recorded at the OCC.
- CCTV with video image feeds to OCC and transit police department that provide visual verification of alarms generated by the access control system.
- Intrusion detection to protect tunnels and other sensitive assets, with data transmitted to and recorded at the OCC.
- For bus systems, AVL is the core application needed for integration with security, safety, and communications devices.
Layer Security to Protect Assets
Agencies should follow a layered approach to protect assets, including the security system itself. If a video surveillance system is installed with images monitored locally in a station and there is no transmission outside the local facility, there are no additional layers of protection available if station personnel are unable to view the monitors.
Secure Digital Networks
Security experts advise that both authentication and encryption techniques are needed to secure digital communications.26 Strong, proven techniques exist to safeguard communications and should be built into security system design.
26Authentication refers to information attached to a message that validates the identity of the sender. Encryption refers to methods of encoding a message so that it is meaningless, unless the recipient has a key needed to decode the message.
Maximize System Robustness
System robustness, or the ability of the system to remain operational under internal or external stress, is necessary for the system to survive not only day-to-day wear and tear and the inevitable system glitches, but also attacks or disasters. System robustness can be increased by including redundant and backup systems in the design and using hardened equipment.
go to top of the page9.6.7 System Implementation
System implementation refers to all of the steps needed to build the system using the architecture and detailed designs produced by processes in the system design process group. Operations and maintenance are also part of this process group.
The outcomes of processes in this group that are especially critical for building integrated systemsinclude:
- Planning for obsolescence
- Early involvement of construction and maintenance
- Technology testing
System security in relation to terrorism The security of transit systems in relation to the emergent threat of terrorist activity is critical for two reasons:
|
Plan for A Five-To Ten-Year Product Obsolescence Cycle
The ability to upgrade information technology and communications systems needs to be built into the planning and implementation of security systems projects. Transit security and information technology specialists report that products often become obsolete and require replacement within a five-to ten-year time frame.
Involve Construction and Maintenance Early in the Process
The construction and maintenance departments should be involved early in the system development process to ensure that all constraints on installation and subsequent maintenance are accounted for prior to installation.
Thoroughly Test Technologies
Transit agency officials place a premium on speedy construction and installation. A thorough testing program may appear to slow down the process and add to costs. However, because the technologies being implemented are new, it is especially critical for the product to be thoroughly tested through installation and into operations to avoid the major costs associated with reworking an inadequate product.
9.7 Effective Transit Security: The Importance of Security Systems Integration
9.7.1 Transit Security
The events of September 11, 2001, brought security to the forefront of transit agency planning concerns, especially in larger cities. Although transit agencies had previously recognized the need to secure their facilities, the lack of any history of such attacks within the U.S., the low probability of an attack against any one transit property, and perennial budget pressures resulted in security countermeasures being given a relatively low priority. While these factors may still be relevant, transit managers must now explicitly address responses to terrorist attacks in their transit system security plans and projects. The focus on security as it pertains to terrorist attacks is closely related to, but does not entirely overlap with, the focus transit systems have maintained on security as it pertains to crime prevention, and safety.
One particular area of concern is that transit agencies need to develop better methods of communicating during emergencies both internally and with emergency responders.
"To effectively do their job, public safety responders depend on sophisticated communication systems to relay mission-critical information in real time. They also require wireless systems that provide immediate channel availability. Today's wireless communications systems must support a growing set of missions, such as responses to weapons of mass destruction and domestic terrorism, requiring coordinated participation from agencies at all levels of government. Unfortunately, in many jurisdictions, public safety agencies operate and maintain largely independent radio systems. This type of deployment is often referred to as the "stovepipe model", where systems are installed to serve the mission of a single agency, and where the individual systems lack the capacity to support interoperability with surrounding support agencies. This type of system deployment can cause potentially dangerous situations that risks lives."27
"The ability of the public safety community to provide a rapid coordinated response to criminal activities, fires, medical emergencies ... natural disaster ... terrorism ... and mass-casualty tragedies ... accentuate the importance of a coordinated response among public safety agencies from all levels of government."
"Foremost among the obstacles that can hinder an effective multi-jurisdictional response is the lack of interoperability among public safety agencies. Wireless interoperability is simply the ability of public safety officials to communicate across different wireless systems when necessary. Radio communications are often public safety personnel's only lifeline when operating in a crisis environment. Without communications interoperability, both life and property are put at significant risk."28
27The Role of States in Public Safety Wireless Interoperability, Public Safety Wireless Network Program.
The Capital Wireless Integrated Network (CapWIN) in the Washington, D.C. metropolitan area and the New York State Integrated Incident Management System (IIMS) are real-time systems to enhance data communications among transportation and public safety agencies systems, especially for the purposes of incident management. While these systems do not focus on transit, the methods and results of these integration efforts are very similar to what would be needed in a transit context.29
29For more information on CapWin, see http://www.capwin.org. For more information on IIMS, see http://www.itspublicsafety.net/law_itsmanagement.htm.
go to top of the page
9.7.2 Systems Integration and Security
In the past two decades, there has been both an evolution and a revolution in the application of technology to everyday life. The evolution is evident in the growing deployment of increasingly sophisticated electronic devices like CCTV, while the technological revolution is seen in the application of high levels of digital computing power, storage capacity, and communications bandwidth to all economic activity, including the transit industry.
As technology assumes a bigger role in various aspects of transit operations, the ability of systems to share information brings increasing benefits to operations as well as to transit security. As noted in Chapter 2, organizations of all kinds tend to build "stovepipe systems." However, a higher level of security is possible when agencies, personnel, and technical components work together.
Systems integration brings a synergistic and inclusive view to systems planning and implementation. The holistic perspective takes into account all of the physical, technical, operational, institutional, and procedural factors that comprise a security system.30 Transit system managers can use these factors to:
- Integrate security devices into a coherent whole
- Integrate security devices into the transit system
- Integrate security and non-security functions
- Interface with non-transit agencies, such as emergency services and traffic management
30FHWA, Chapter 16, "Regional Integration," Freeway Management and Operations Handbook, (Publication Number FHWA-OP-04-003) http://ops.fhwa.dot.gov/Travel/traffic/freeway_management.htm.
Integration contributes to transit security by allowing security systems to generate data that can be used for real-time, system-wide decision support.
The three main benefits of systems integration to a transit security system include:
- Improving communications. An integrated system can communicate timely information to organizational units. The information used by or generated by integrated devices can be communicated to other devices and to decision-makers. With an integrated system, a person or technology is always collecting and transmitting information to other organizational units .
- Leveraging resources. One technological device or system can have multiple purposes. Integrated systems leverage the data being monitored, collected, and transmitted among multiple functions, and multiple organizations. These organizations can share the cost of system implementation and operation. For example, technology to deter, prevent, detect, and respond to terrorist attacks is related to technology applications for crime prevention and safety .
- Promoting standards usage: As discussed in Section 9.4.3, the need for systems integration promotes the use of standards, which produces other secondary benefits for the transit operator. Information technology and telecommunications standards are expected to lead to the interoperability and interchangeability of technical devices, facilitated upgrades to new technology, accurate data transfers, and lower long-term costs.
|
NEWSLETTER
|
| Join the GlobalSecurity.org mailing list |
|
|
|

